If you import a 3rd get together library, do you overview each line of code? Most software program packages rely upon exterior libraries, trusting that these packages aren’t doing something surprising. If that belief is violated, the results could be enormous—no matter whether or not the package deal is malicious, or well-intended however utilizing overly broad permissions, reminiscent of with Log4j in 2021. Provide chain safety is a rising problem, and we hope that larger transparency into package deal capabilities will assist make safe coding simpler for everybody.
Avoiding dangerous dependencies could be arduous with out acceptable info on what the dependency’s code truly does, and reviewing each line of that code is an immense process. Each dependency additionally brings its personal dependencies, compounding the necessity for overview throughout an increasing net of transitive dependencies. However what if there was a straightforward technique to know the capabilities–the privileged operations accessed by the code–of your dependencies?
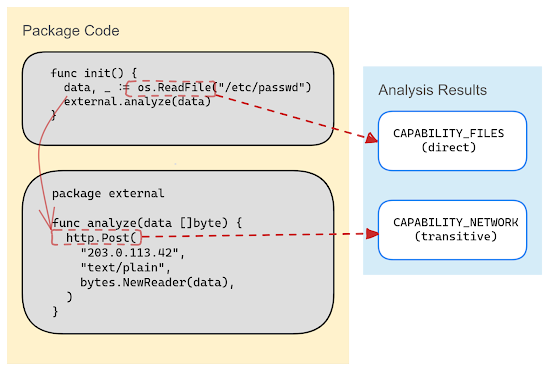
Capslock is a functionality evaluation CLI instrument that informs customers of privileged operations (like community entry and arbitrary code execution) in a given package deal and its dependencies. Final month we printed the alpha model of Capslock for the Go language, which might analyze and report on the capabilities which might be used beneath the floor of open supply software program.
This CLI instrument will present deeper insights into the habits of dependencies by reporting code paths that entry privileged operations in the usual libraries. In upcoming variations we’ll add assist for open supply maintainers to prescribe and sandbox the capabilities required for his or her packages, highlighting to customers what capabilities are current and alerting them if they alter.
Capabilities vs Vulnerabilities
Vulnerability administration is a crucial a part of your provide chain safety, but it surely doesn’t offer you a full image of whether or not your dependencies are secure to make use of. Including functionality evaluation into your safety posture, provides you a greater concept of the varieties of habits you possibly can count on out of your dependencies, identifies potential weak factors, and lets you make a extra knowledgeable selection about utilizing a given dependency.
Capslock is motivated by the assumption that the precept of least privilege—the concept that entry needs to be restricted to the minimal set that’s possible and sensible—needs to be a first-class design idea for safe and usable software program. Utilized to software program growth, because of this a package deal needs to be allowed entry solely to the capabilities that it requires as a part of its core behaviors. For instance, you wouldn’t count on an information evaluation package deal to want entry to the community or a logging library to incorporate distant code execution capabilities.
Capslock is initially rolling out for Go, a language with a sturdy safety dedication and incredible tooling for locating identified vulnerabilities in package deal dependencies. When Capslock is used alongside Go’s vulnerability administration instruments, builders can use the extra, complementary alerts to tell how they interpret vulnerabilities of their dependencies.
These functionality alerts can be utilized to
-
Discover code with the very best ranges of entry to prioritize audits, code opinions and vulnerability patches
-
Evaluate potential dependencies, or search for different packages when an present dependency is not acceptable
-
Floor undesirable functionality utilization in packages to uncover new vulnerabilities or determine provide chain assaults in progress
-
Monitor for surprising rising capabilities as a result of package deal model or dependency adjustments, and even combine functionality monitoring into CI/CD pipelines
-
Filter vulnerability knowledge to reply to essentially the most related instances, reminiscent of discovering packages with community entry throughout a network-specific vulnerability alert
Utilizing Capslock
We’re trying ahead to including new options in future releases, reminiscent of higher assist for declaring the anticipated capabilities of a package deal, and increasing to different programming languages. We’re working to use Capslock at scale and make functionality info for open supply packages broadly accessible in numerous neighborhood instruments like deps.dev.
You’ll be able to attempt Capslock now, and we hope you discover it helpful for auditing your exterior dependencies and making knowledgeable selections in your code’s capabilities.
We’ll be at Gophercon in San Diego on Sept twenty seventh, 2023—come and chat with us!