Traditionally, risk actors weren’t eager to interact with journalists. They might have adopted press protection about themselves, in fact, however they hardly ever courted such consideration; staying beneath the radar was normally way more essential to them. The concept of attackers recurrently placing out press releases and statements – not to mention giving detailed interviews and arguing with reporters – was absurd (even when they had been generally very prepared to publicly argue with one another).
After which got here the ransomware gangs.
Ransomware has modified many aspects of the risk panorama, however a key current growth is its growing commoditization and professionalization. There’s ransomware-as-a-service; logos and branding (and even paying acolytes to get tattoos) and slick graphics on leak websites; outlined HR and Authorized roles; and bug bounty programmes. Accompanying all this – alongside the astronomical prison positive aspects and the distress heaped on innumerable victims – is a slew of media consideration, and an more and more media-savvy assortment of risk actors.
Removed from shying away from the press, as so many risk actors did prior to now, some ransomware gangs have been fast to grab the alternatives it affords them. Now, risk actors write FAQs for journalists visiting their leak websites; encourage reporters to get in contact; give in-depth interviews; and recruit writers. Media engagement gives ransomware gangs with each tactical and strategic benefits; it permits them to use stress to their victims, whereas additionally enabling them to form the narrative, inflate their very own notoriety and egos, and additional ‘mythologize’ themselves.
In fact, it’s not at all times a harmonious relationship. Lately, we’ve seen a number of examples of ransomware actors disputing journalists’ protection of assaults, and making an attempt to appropriate the document – generally throwing insults at particular reporters into the discount. Whereas this has implications for the broader risk panorama, it additionally has ramifications for particular person targets. Along with coping with enterprise impacts, ransom calls for, and reputational fallout, organizations at the moment are compelled to look at as ransomware gangs scrap with the media within the public area – with each incident fuelling extra protection and including additional stress.
Sophos X-Ops performed an investigation of a number of ransomware leak websites and underground prison boards to discover how ransomware gangs are searching for to leverage the media and management the narrative – thereby hacking not solely programs and networks, but additionally the accompanying publicity.
A quick abstract of our findings:
- Ransomware gangs are conscious that their actions are thought-about newsworthy, and can leverage media consideration each to bolster their very own ‘credibility’ and to exert additional stress on victims
- Risk actors are inviting and facilitating communications with journalists through FAQs, devoted non-public PR channels, and notices on their leak websites
- Some ransomware gangs have given interviews to journalists, by which they supply a largely optimistic perspective of their actions – doubtlessly as a recruitment device
- Nonetheless, others have been extra hostile to what they see as inaccurate protection, and have insulted each publications and particular person journalists
- Some risk actors are more and more professionalizing their strategy to press and reputational administration: publishing so-called ‘press releases’; producing slick graphics and branding; and searching for to recruit English writers and audio system on prison boards
Our goals in publishing this piece are to discover how and to what extent ransomware gangs are growing their efforts on this space, and to counsel issues that the safety neighborhood and the media can do now to negate these efforts and deny ransomware gangs the oxygen of publicity they’re searching for:
- Chorus from partaking with risk actors until it’s within the public curiosity or gives actionable data and intelligence for defenders
- Present data solely to help defenders, and keep away from any glorification of risk actors
- Assist journalists and researchers focused by attackers
- Keep away from naming or crediting risk actors until it’s purely factual and within the public curiosity
Leveraging the media
Ransomware gangs are very aware that the press considers their actions newsworthy, and can generally hyperlink to current protection of themselves on their leak websites. This reinforces their ‘credentials’ as a real risk for the advantage of guests (together with reporters and new victims) – and, in some circumstances, is probably going an ego journey as properly.
Determine 1: Vice Society thanks a selected journalist for an article by which it was a part of a ‘Prime 5’ of ransomware and malware teams in 2022
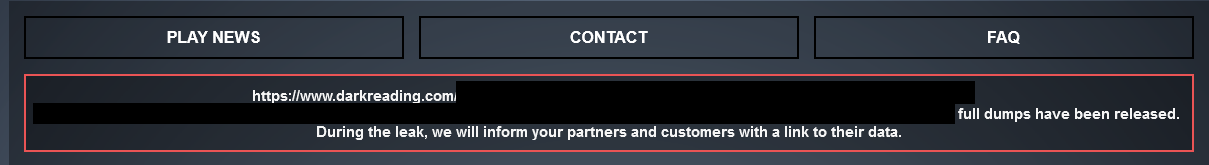
Determine 2: The Play ransomware group hyperlinks to a Darkish Studying article on its leak website
However some ransomware gangs aren’t content material with merely posting current protection; they’ll additionally actively solicit journalists.
Collaboration
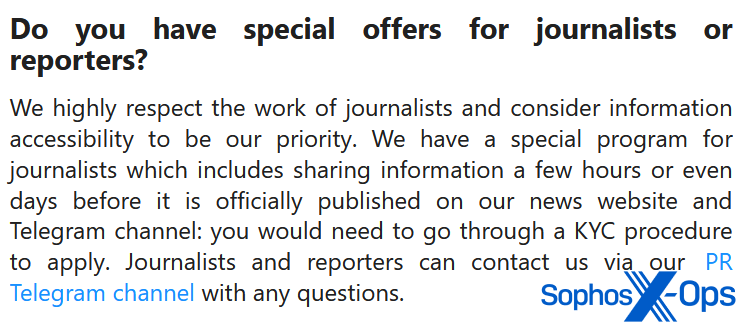
The RansomHouse group, for instance, has a message on its leak website particularly geared toward journalists, by which it provides to share data on a ‘PR Telegram channel’ earlier than it’s formally revealed. It’s not alone on this; allegedly, the LockBit ransomware group communicates with journalists utilizing Tox, an encrypted messaging service (many ransomware gangs listing their Tox ID on their leak websites).
Determine 3: An invite from RansomHouse
Determine 4: The RansomHouse PR Telegram channel
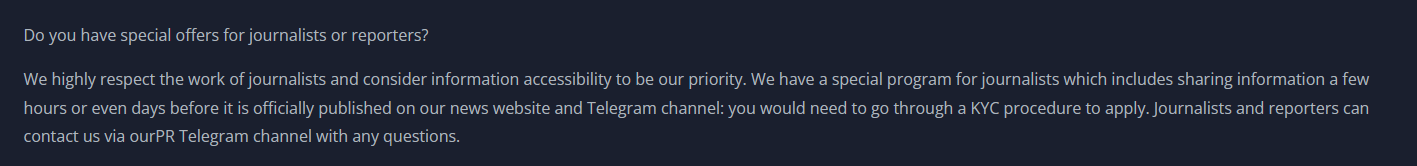
The 8Base leak website has an an identical message (as different researchers have famous, 8Base and RansomHouse share different similarities, together with their phrases of service and ransom notes).
Determine 5: 8Base’s message to journalists
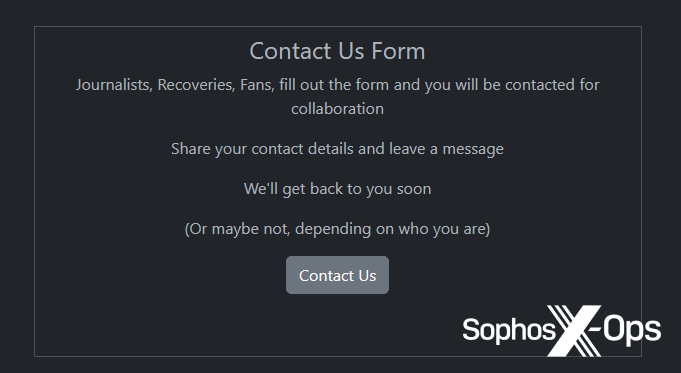
Rhysida’s contact kind on its leak website addresses a number of teams of individuals. Curiously, journalists seem first on this listing, earlier than ‘Recoveries’ (presumably referring to victims or individuals engaged on their behalf).
Determine 6: Rhysida’s contact kind
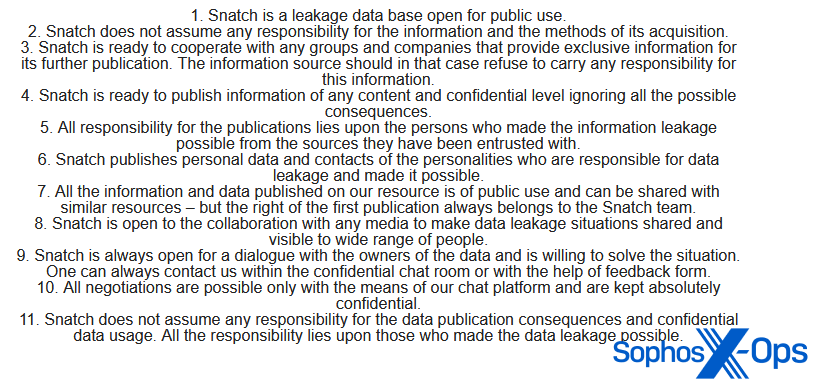
Over on the Snatch leak website, the risk actor maintains a “Public discover.” Of explicit observe is quantity eight on this listing: “Snatch is open to the [sic] collaboration with any media to make knowledge leakage conditions shared [sic] and visual to large [sic] vary of individuals.” And, as with Rhysida, journalists come earlier than sufferer negotiations on the listing.
Determine 7: Snatch’s ‘Public discover’
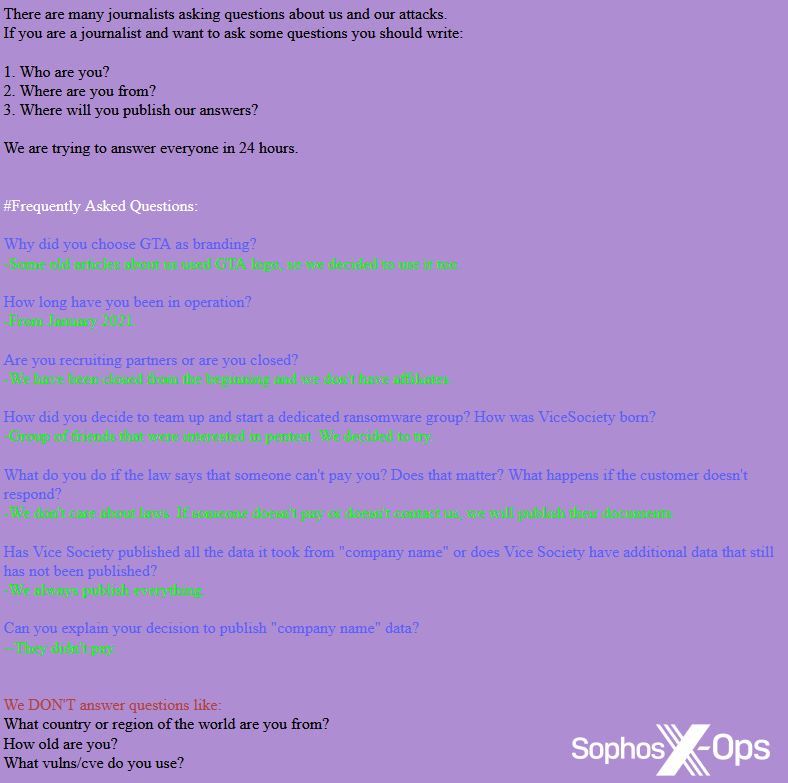
On Vice Society’s leak website, the risk actor notes: “There are numerous journalists asking questions on us and our assaults.” The message goes on to incorporate a full FAQ for reporters, together with a request for journalists to supply their title and outlet, and particulars of questions the group gained’t reply. Helpfully, for reporters with urgent deadlines, the risk actor additionally states that they fight to reply to queries inside 24 hours – an instance {of professional} PR finest apply, which demonstrates how essential that is to the risk actor.
Determine 8: Vice Society’s FAQ for journalists
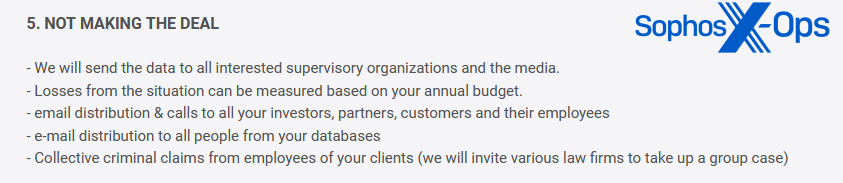
As famous earlier, a lot of that is possible carried out for bragging rights and to bolster criminals’ credibility and notoriety (which, in flip, can not directly enhance the stress on victims). However some teams are extra specific; Dunghill Leak, for instance, warns victims that if they don’t pay, they’ll take a number of actions – together with sending knowledge to the media.
Determine 9: Dunghill Leak’s warning to victims, together with a risk to ship knowledge to the media
Whereas not inside the scope of this text, the final line is price noting as properly: Dunghill threatens to “invite varied legislation corporations to take up a gaggle case.” Ransomware class motion lawsuits aren’t unprecedented, and should develop into more and more frequent.
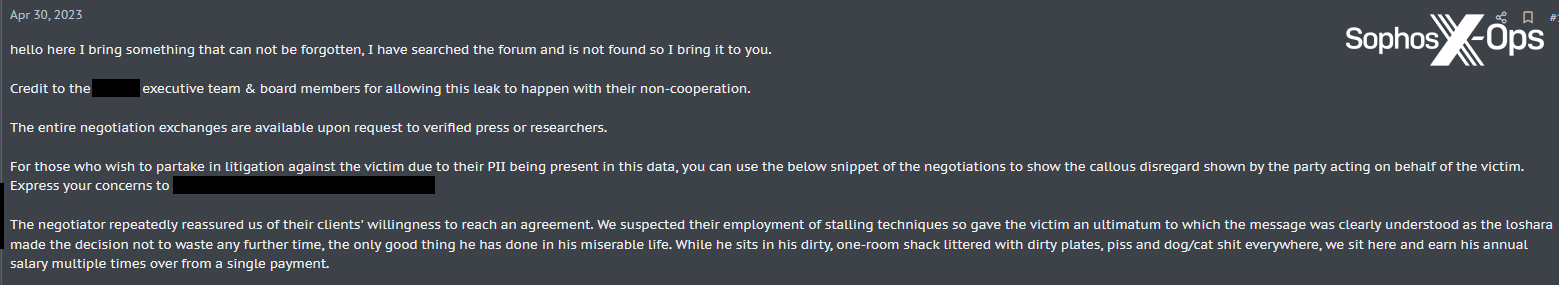
In an analogous vein, we noticed a consumer posting on a outstanding prison discussion board about an organization which had been the sufferer of an information breach. The consumer acknowledged that negotiations had damaged down, and provided to supply “all the negotiation exchanges” to “verified press or researchers” – and in addition famous that “for individuals who want to partake in litigation…you should utilize the beneath snippet of the negotiations.” This is among the methods by which ransomware actors are shifting their methods, utilizing multi-pronged weaponization (publicity, lawsuits, regulatory obligations) to exert additional stress on victims. For example, ALPHV/BlackCat lately reported a sufferer to the Securities and Change Fee (SEC) for not disclosing a breach – one thing which some commentators consider could develop into more and more frequent.
Determine 10: A publish on a prison discussion board, concerning an information breach
Different ransomware gangs are very conscious that they will exert extra stress on victims by elevating the spectre of media curiosity. Our Managed Detection and Response (MDR) workforce lately noticed ransom notes containing this risk from each Inc (“confidential knowledge…may be unfold out to individuals and the media”) and Royal (“anybody on the web from darknet criminals…journalists…and even your staff will be capable to see your inner documentation”).
Not all ransom notes point out the media, in fact, and plenty of ransomware gangs preserve minimalist, bare-bones leak websites which merely listing their victims, with no direct appeals to journalists. However others interact instantly with the media, within the type of interviews.
Interviews
A number of ransomware actors have given in-depth interviews to journalists and researchers. In 2021, the LockBit operators granted an interview to Russian OSINT, a YouTube and Telegram channel. The identical 12 months, an nameless REvil affiliate spoke to Lenta.ru, a Russian-language on-line journal. In 2022, Mikhail Matveev (a.okay.a. Wazawaka, a.okay.a. Babuk, a.okay.a. Orange), a ransomware actor and founding father of the RAMP ransomware discussion board, spoke intimately to The Document – and even supplied an image of himself. And some weeks later, a founding member of LockBit spoke to vx-underground (by which they admitted that they personal three eating places in China and two in New York.
In most of those interviews, the risk actors appear to relish the chance to present insights into the ransomware ‘scene’, talk about the illicit fortunes they’ve amassed, and supply ‘thought management’ concerning the risk panorama and the safety business. Just one – the REvil affiliate – provides a largely unfavourable depiction of the prison life (“…you’re afraid on a regular basis. You get up in worry, you go to mattress in worry, you disguise behind a masks and a hood in a retailer, you even disguise out of your spouse or girlfriend”).
So, along with the motivations we’ve already mentioned – notoriety, egotism, credibility, not directly growing stress on victims – an additional doable cause for engagement with the media is recruitment. By depicting ransomware exercise as a glamorous, rich enterprise (“the chief in monetization,” as Matveev places it), risk actors may very well be making an attempt to draw extra members and associates.
Press releases and statements
A handful of ransomware teams challenge what they name “press releases” – and the truth that they use this time period is telling in itself. Karakurt, for instance, maintains a separate web page for its press releases. Of the three presently revealed, one is a public announcement that the group is recruiting new members, and the others are about particular assaults. In each these latter circumstances, based on Karakurt, negotiations broke down, and the so-called ‘press releases’ are in actual fact thinly-veiled assaults on each organizations in an try and stress them into paying and/or trigger reputational harm.
Each these items, whereas containing the odd error or idiosyncratic phrasing, are written in remarkably fluent English. One, aping the fashion of real press releases, even incorporates a direct quote from “the Karakurt workforce.”
Determine 11: Karakurt’s ‘Press Releases’ web page
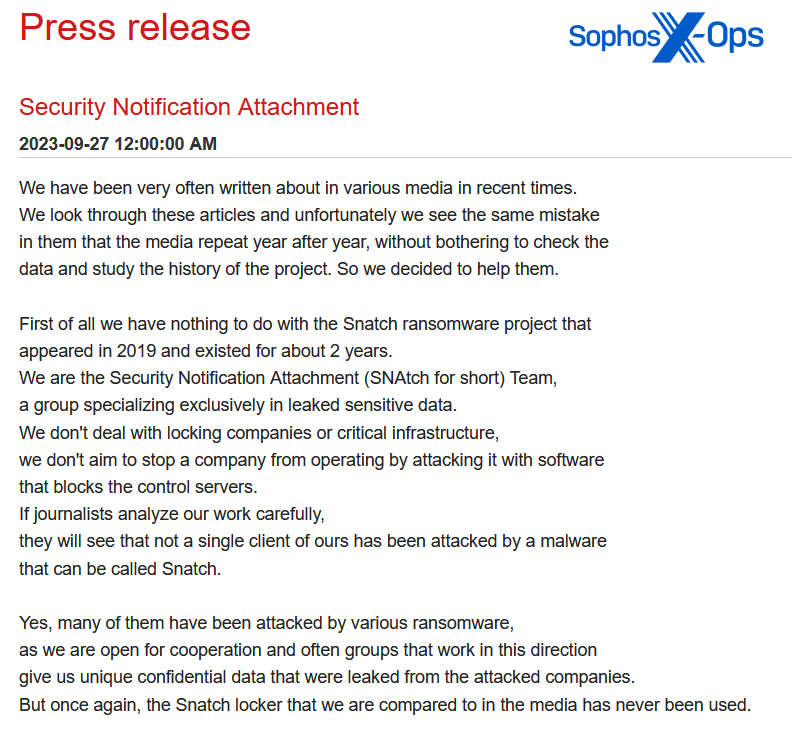
In distinction, an instance of a press launch from the Snatch group is far much less fluent, and doesn’t concentrate on a selected sufferer. As a substitute, it’s geared toward correcting errors by journalists (one thing that we’ll talk about in additional element shortly).
Determine 12: An excerpt from Snatch’s ‘press launch’
This assertion ends with the next sentence: “We’re at all times open for cooperation and communication and when you have any questions we’re able to reply them right here in our tg [Telegram] channel.”
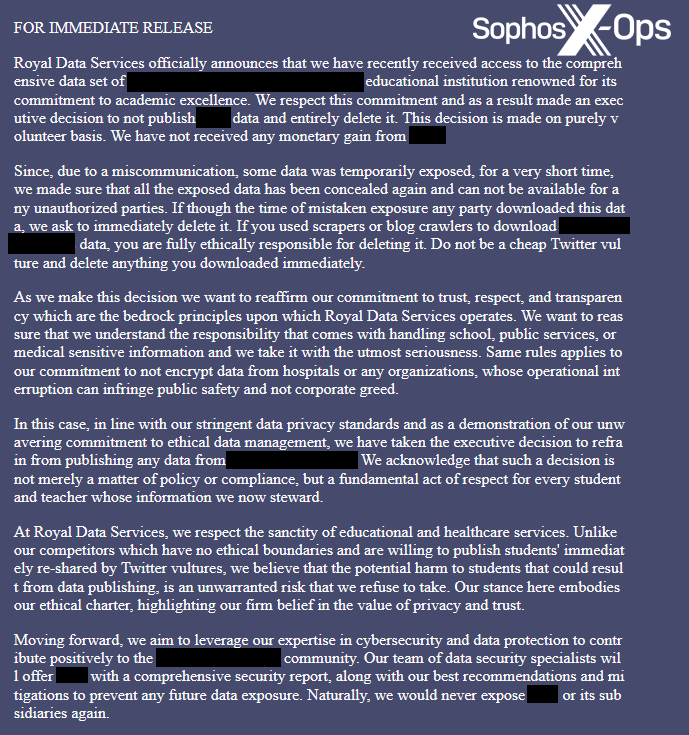
An additional instance, this one from Royal (not formally titled as a press launch, however with the heading “FOR IMMEDIATE RELEASE”), declares that the group is not going to publish knowledge from a selected sufferer (a college), however will as a substitute delete it “consistent with our stringent knowledge privateness requirements and as an indication of our unwavering dedication to moral knowledge administration.” Right here, the risk actor is arguably inviting a comparability between their very own proactive motion to ‘shield’ towards the leak (for which they’re accountable) and the mishandling of ransomware incidents and delicate knowledge by some organizations – thereby aiming to painting itself as extra accountable {and professional} than a few of its victims.
Determine 13: A public assertion by the Royal ransomware group
What’s notably noteworthy right here is the language; a lot of the fashion and tone of this announcement will probably be recognisable to anybody who’s handled press releases and public statements. For example: “the bedrock rules upon which Royal Knowledge Providers operates”; “At Royal Knowledge Providers, we respect the sanctity of academic and healthcare companies”; “Transferring ahead, we purpose to…”.
It’s additionally price noting that Royal appears to be making an attempt to rebrand itself as a safety service (“Our workforce of knowledge safety specialists will provide…a complete safety report, together with our greatest suggestions and mitigations…”). It has this in frequent with many different ransomware teams – who, in wholly unconvincing makes an attempt to painting themselves as forces for good, have referred to themselves as a “penetration testing service” (Cl0p); “trustworthy and easy pentesters” (8Base); or as conducting “a cybersecurity research” (ALPHV/BlackCat).
Rebranding is one other PR tactic borrowed from official business, and it’s not unreasonable to invest that ransomware teams could step up this tactic sooner or later – maybe as a recruitment device, or to try to alleviate unfavourable protection from the media and a focus from legislation enforcement.
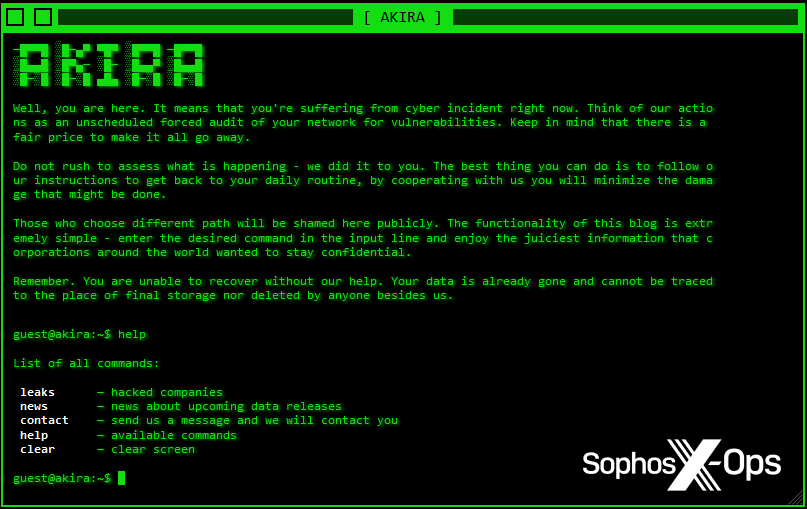
Branding
Branding is vastly essential to ransomware gangs searching for press protection. Catchy names and slick graphics assist entice the eyes of journalists and readers – notably relating to leak websites, as they’re the public-facing presences of those risk actors, and will probably be steadily visited by journalists, researchers, and victims. Contemplate Akira, with its retro aesthetics and interactive terminal, or Donut Leaks, which has a frontpage graphic full with flickering neon indicators.
Determine 14: The Akira leak website
Determine 15: The Donut Leaks website
The LostTrust ransomware group (a doable rebrand of MetaEncryptor) is so patently conscious that its leak website is its level of contact with the broader world, that it opted for a press convention graphic on its homepage.
Determine 16: LostTrust’s leak website. Notice the blurb on the backside, which incorporates the warning that “each incident is notified to all doable press within the area” – echoing the warning from Dunghill Leak
On the opposite aspect of the coin, one ransomware group – both fed up with this pattern, or getting performatively meta with it – determined to eschew a reputation and model altogether.
Determine 17: A ransomware group which refuses to present itself a reputation – resulting in it inevitably being named ‘NoName ransomware’
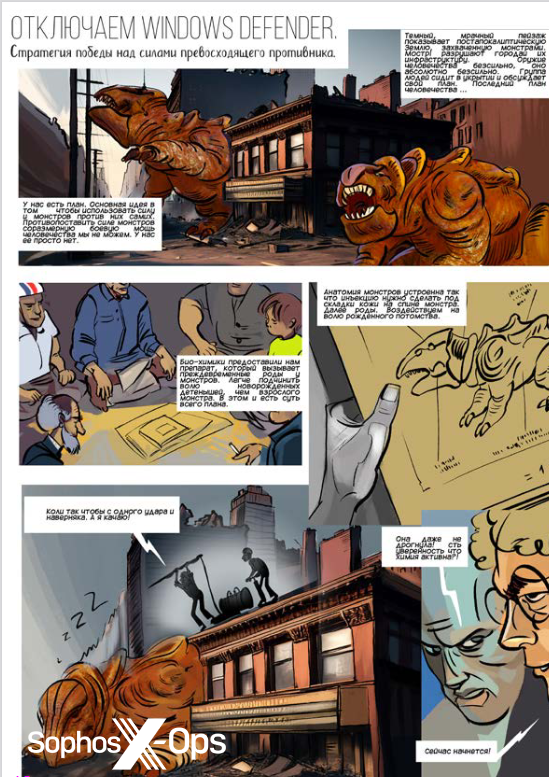
Refined branding isn’t unique to ransomware gangs, in fact, and speaks to a wider level concerning the growing professionalization throughout many classes of risk actor, as we famous in our 2023 Annual Risk Report. Trendy adverts for malware merchandise, for instance, are sometimes characterised by enticing graphics and high-quality design.
One outstanding prison discussion board – which beforehand ran common, well-established ‘analysis contests’ – even has its personal ezine, together with artwork, tutorials, and interviews with risk actors. An instance, maybe, of cybercriminals not solely partaking with media shops, however creating their very own.
Determine 18: Artwork from an ezine produced by members of a prison discussion board
Recruitment
When a Ukrainian researcher leaked hundreds of messages from contained in the Conti ransomware gang in March 2022, many had been shocked on the extent of group inside the group. It had a definite hierarchy and construction, very similar to a official firm: bosses, sysadmins, builders, recruiters, HR, and Authorized. It paid salaries recurrently, and set working hours and holidays. It even had bodily premises. However what’s notably fascinating within the context of this text is that Conti had not less than one individual (and presumably as many as three) devoted to negotiating ransoms and writing ‘weblog posts’ for the leak website (a ‘weblog’ is a euphemism for an inventory of victims and their revealed knowledge). So the kinds of issues we’ve been discussing – responding to journalists, writing press releases, and so forth – aren’t essentially simply cobbled collectively by hackers after they’re not busy hacking. Inside outstanding, well-established teams, they might properly add as much as a full-time function – mirroring the state of affairs in expertise and safety corporations, with groups devoted to publicizing analysis and outcomes (Sophos X-Ops being an instance, if that’s not getting too meta).
Whereas many ransomware-related actions don’t require fluent English abilities, this type of work does – particularly if risk actors are additionally going to be writing public statements. Such people should be recruited from someplace, and on prison boards, adverts for English audio system and writers (and, often, audio system of different languages) are pretty frequent. Many of those advertisements aren’t essentially for ransomware teams, in fact, however possible for social engineering/scamming/vishing campaigns.
Determine 19: An advert on a prison discussion board for “ English caller.” This advert might be for some form of rip-off marketing campaign
In different circumstances, the type of work being provided is much less clear, and requires writers slightly than audio system:
Determine 20: A consumer on a prison discussion board seeks a “Skilled English Author”
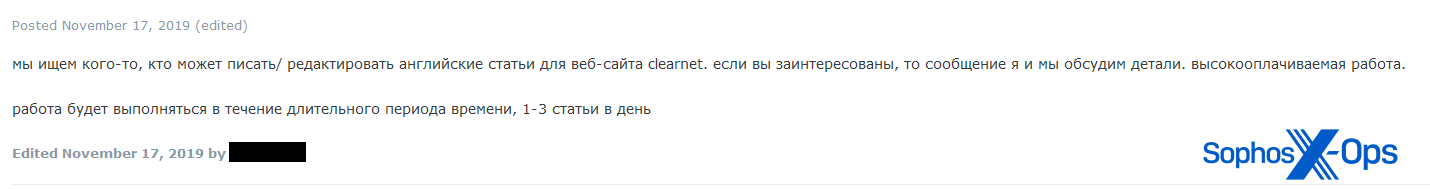
Determine 21: A job advert on a prison discussion board. Trans.: “We’re on the lookout for somebody who can write/edit English articles for the clearnet web site. If you’re , message me and we’ll talk about the main points. excessive paying job. the work will probably be accomplished over a protracted time frame, 1-3 articles per day.” The identical consumer additionally marketed for a “journalist/author.”
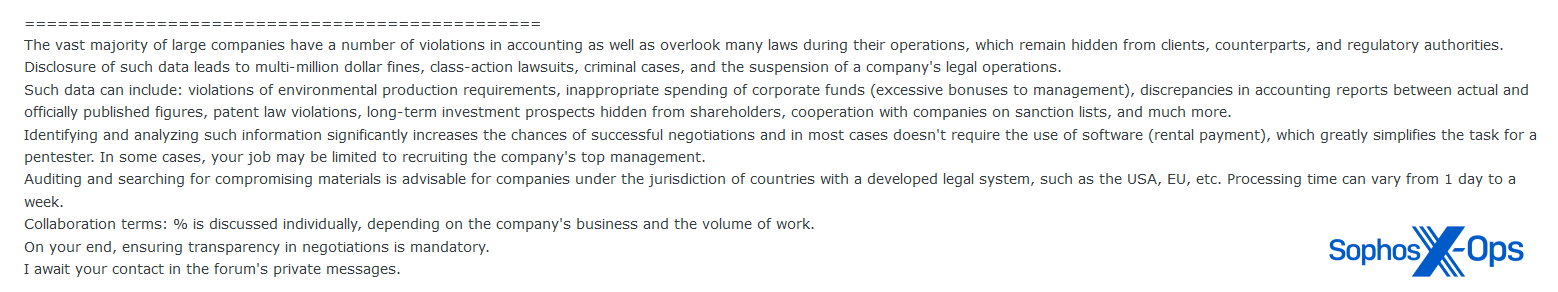
In a very curious instance – albeit one not associated to the media – a consumer created a thread entitled: “Evaluation of economic and authorized vulnerabilities for negotiations”:
Determine 22: An excerpt from the consumer’s publish
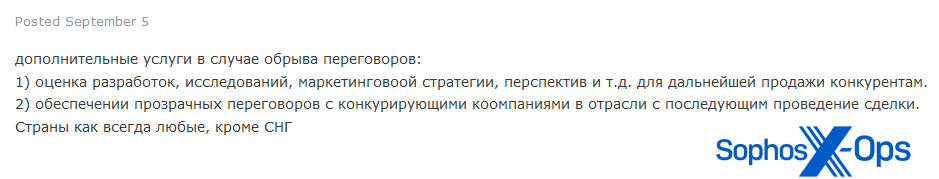
In the identical thread, the consumer later added extra element – noting that different duties would come with (trans.) “add bigdata to the onion area”, and that “in case of breakdown of negotiations”, candidates would even be anticipated to carry out “evaluation of developments, analysis, advertising technique, prospects, and so forth. for additional sale to rivals.”
Determine 23: Additional element from the identical consumer
We assess that that is possible an try and recruit somebody to assist extort corporations into paying a ransom, by discovering compromising data which risk actors may use to use stress throughout negotiations. Notice that the primary a part of the advert states “generally [this] doesn’t require using software program”, implying that this isn’t a ‘conventional’ ransomware group utilizing encrypting malware.
Lastly, we additionally famous a number of situations of customers promoting their companies as translators, notably Russian to English and vice versa.
Determine 24: A consumer provides their companies as a translator
Whereas we didn’t discover any particular examples of risk actors making an attempt to recruit individuals with advertising/PR expertise, that is one thing we’re going to maintain an eye fixed out for. Given the growing ‘celebrification’ of ransomware teams (see LockBit’s tattoo stunt and comparable developments) and the rebranding methods mentioned beforehand, it could solely be a matter of time earlier than criminals make extra concerted efforts to handle their public photographs and cope with the growing quantities of media consideration they obtain.
When issues go unsuitable
We’ve famous that ransomware teams leverage the media in plenty of methods: referring to earlier protection on their leak websites; inviting questions from journalists; giving interviews; and utilizing the specter of publicity to coerce victims into paying ransoms. Nonetheless, as many public figures and corporations have came upon to their price, relationships with the media aren’t at all times affable. On a number of events, ransomware teams and different risk actors have criticized journalists for what they really feel is inaccurate or unfair protection.
The builders of WormGPT, for instance – a derivation of ChatGPT, provided on the market on prison marketplaces to be used by risk actors – shut their undertaking down, because of the quantity of media scrutiny. In a discussion board publish, they acknowledged: “we’re more and more harmed by the media’s portrayal…Why do they try and tarnish our status on this method?”
Ransomware teams, however, are usually extra aggressive of their rebuttals. ALPHV/BlackCat, as an illustration, revealed an article on its leak website entitled “Assertion on MGM Resorts Worldwide: Setting the document straight”, a 1,300-word publish by which it criticized plenty of shops for not checking sources and reporting incorrect data.
Determine 25: ALPHV/BlackCat criticizes an outlet for ‘false reporting’
Determine 26: ALPHV/BlackCat criticizes one other outlet for ‘false reporting’, whereas admitting that it beforehand falsely reported a supply of ‘false data’
The assertion goes on to assault a person journalist and a researcher, earlier than concluding: “we now have not spoken with any journalists…We didn’t and probably gained’t.” Curiously, then, that is an instance of a ransomware group not partaking with the media – as a substitute making an attempt to regulate the narrative by presenting itself as the only real, dominant, voice of fact. (Most likely there are some energy dynamics at play right here, too, however digging into the psychology of ransomware actors is one thing we’re neither certified nor inclined to do.)
The Cl0p ransomware group tried to do one thing comparable throughout a rash of high-profile assaults earlier this 12 months, which leveraged a vulnerability within the MOVEit file-transfer system. In a publish on its leak website, it acknowledged that “all media talking about this are do [sic] what they at all times do. Present little fact in an enormous lie.” Later, the group particularly referred to as out the BBC for “creating propaganda,” after Cl0p had emailed the BBC with data. Very like the ALPHV/BlackCat instance above, Cl0p is making an attempt to ‘set the document straight,’ correcting what it sees as inaccuracies in media protection and representing itself as the one authoritative supply of data. The message to victims, researchers, and the broader public: don’t consider what you learn within the press; solely we now have the true story.
Determine 27: The Cl0p ransomware gang calls out the BBC for ‘twisting’ data
An uneasy relationship
Cl0p isn’t alone in feeling mistrustful of journalists; it’s a typical sentiment on prison boards. Many risk actors – not simply ransomware teams – dislike the press, and a few non-ransomware criminals are skeptical of the connection between journalists and ransomware gangs:
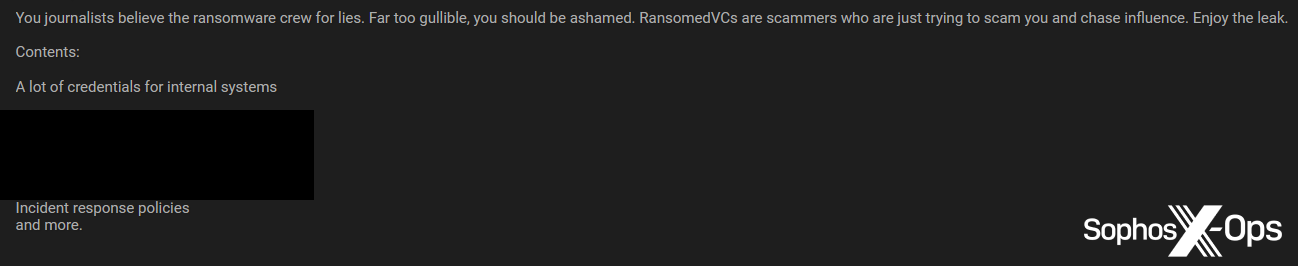
Determine 28: A risk actor criticizes journalists for believing the “lies” of ransomware actors, and criticizes ransomware actors “who’re simply making an attempt to rip-off you [journalists] and chase affect.” Notice that the sentiment right here shouldn’t be dissimilar to that expressed by ALPHV/BlackCat and Cl0p within the earlier part
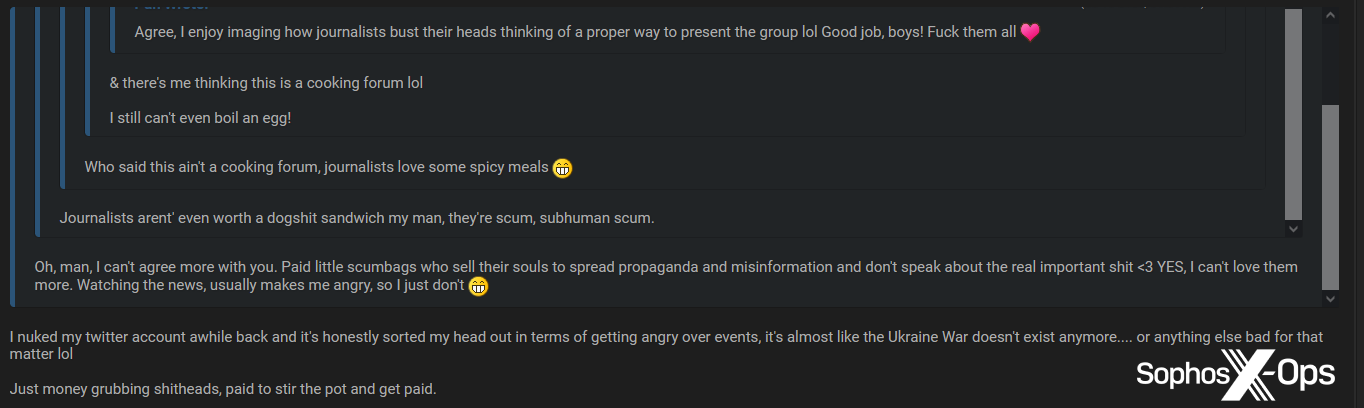
Simply as ransomware teams are aware that their leak websites are frequented by journalists, so members of prison boards know that journalists have infiltrated their websites. Excessive-traffic threads about outstanding breaches and incidents will generally comprise feedback alongside the strains of ‘Right here come the reporters,’ which often descend into full-blown rants and insults.
Determine 29: A number of members of a prison discussion board insult journalists
Extra hardly ever, risk actors will name out and/or assault particular person journalists, as within the ALPHV/BlackCat instance above. Whereas this hasn’t, to our information, escalated to direct threats, these reactions are possible designed to make the journalists in query really feel uncomfortable, and in some circumstances to trigger reputational harm – not at all times efficiently.
The title and branding of the carding market Brian’s Membership, for instance, relies on safety journalist Brian Krebs. The location makes use of Krebs’ picture, first title, and a play on his surname (‘Krabs’, or crabs, for ‘Krebs’), on each its homepage and inside the website itself.
Whereas this doesn’t appear to unduly concern Krebs (he mentions being “shocked and delighted” to obtain a reply from the Brian’s Membership admin after making an enquiry about the location being compromised; the admin’s reply started: “No. I’m the true Brian Krebs right here 😊”), different journalists may not really feel fairly so relaxed on this state of affairs.
In fact, researchers aren’t immune to those techniques both, and are additionally typically topic to insults and threats on boards. The connection between risk actors and researchers is a complete different story, and out of scope for this text, however one instance is price noting. After publishing the primary a part of a three-part collection on the interior workings of the LockBit gang, researcher Jon DiMaggio was alarmed to find that LockBit’s profile image on a outstanding prison discussion board had been modified to a photograph of himself.
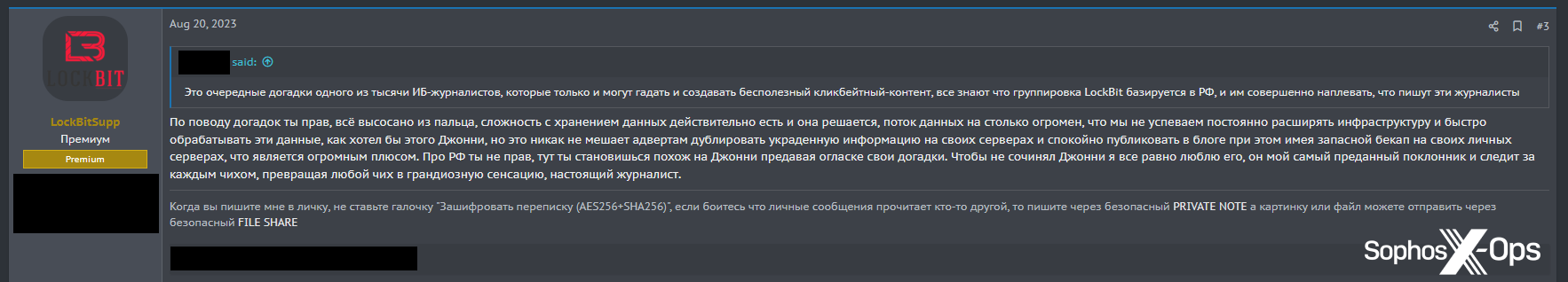
After publication of the ultimate a part of the collection, risk actors mentioned the report amongst themselves. One was dismissive (trans.: “These are simply the most recent guesses from one of many hundreds of data safety journalists who can solely guess and create ineffective clickbait content material”), to which the LockBit account replied: “you’re proper, all the pieces is made up…[but] it doesn’t matter what Johnny says, I nonetheless love him, he’s my most devoted fan and follows each sneeze, turning any sneeze into an enormous sensation, an actual journalist.”
Determine 31: LockBit posts in a dialogue about DiMaggio’s experiences
So even LockBit – one of the vital outstanding ransomware gangs, which has devoted vital effort and time into cultivating its picture, professionalizing itself, and giving media interviews – is sceptical of journalists and their motivations.
Conclusion
The truth that some ransomware teams will eagerly solicit media protection and talk with journalists, regardless of being mistrustful and demanding of the press usually, is a contradiction which will probably be acquainted to many public figures. In the identical method, many journalists will acknowledge the sensation of getting qualms concerning the actions, ethics, and motivations of many public figures, whereas additionally understanding that reporting on these figures is within the public curiosity.
And, prefer it or not, some ransomware actors are on their method to changing into public figures. Accordingly, they’re devoting an growing period of time to ‘managing the media.’ They’re conscious of protection about themselves, and publicly appropriate inaccuracies and omissions. They encourage questions, and supply interviews. They’re aware that cultivating media relationships is beneficial for attaining their very own targets and refining their public picture.
That is, in some methods, distinctive to ransomware gangs. In contrast to just about all different sorts of risk – that are based mostly on going undetected for so long as doable, and ideally indefinitely – a ransomware marketing campaign should ultimately make itself identified to the sufferer, to demand a ransom. Leak websites have to be publicly out there, in order that the criminals can apply stress to victims and publish stolen knowledge. These components, and the explosive development of the ransomware risk, have led to a state of affairs the place risk actors, removed from shunning the more and more shiny glare of the media highlight, acknowledge the potential to replicate and redirect it for their very own ends. They will leverage alternatives to instantly and not directly apply stress to victims; entice potential recruits; enhance their very own notoriety; handle their public picture; and form the narrative of assaults.
In the mean time, these developments are nascent. Whereas there may be actually an effort amongst some ransomware actors to mimic the environment friendly ‘PR machines’ of official companies, their makes an attempt are sometimes crude and amateurish. Typically they appear extra of an afterthought than the rest.
Nonetheless, there are indications that that is altering. Initiatives comparable to devoted PR Telegram channels, FAQs for journalists, and makes an attempt to recruit journalists/writers, could develop and evolve. And as with many elements of ransomware – and the risk panorama usually – commodification and professionalization are on the rise. It could be a method off, nevertheless it’s not unfeasible that sooner or later, ransomware teams could have devoted, full-time PR groups: copywriters, spokespeople, even picture consultants. This will likely present some ‘nice-to-haves’ for ransomware actors – inflating egos, bolstering recruitment efforts – however it’ll predominantly come right down to including to the already vital stress positioned on victims, and decreasing any stress on themselves from legislation enforcement or the prison neighborhood.
Within the meantime, it’s possible that ransomware teams will proceed to attempt to management the narratives round particular person assaults, as we’ve seen lately with Cl0p and ALPHV/BlackCat. We’ll be holding a detailed eye on developments on this house.
Acknowledgments
Sophos X-Ops wish to thank Colin Cowie of Sophos’ Managed Detection and Response (MDR) workforce for his contribution to this text.