Cryptocurrency-based crime has metastasized into many kinds. Due to the convenience with which cryptocurrency ignores borders and permits multinational crime rings to shortly receive and launder funds, and due to widespread confusion about how cryptocurrency features, a variety of confidence scams have targeted on convincing victims to transform their private financial savings to crypto—after which separate them from it.
Amongst these types of organized felony actions, none appear as pervasive as “pig butchering” (from the Mandarin time period, sha zhu pan, coined to explain the exercise). Most of those scams use courting purposes or different social media to lure victims into what they suppose is a budding romantic or platonic relationship, after which introduce a fraudulent scheme to earn money collectively. In some current instances we discovered the scammers utilizing generative AI to jot down messages to their targets to make them extra convincing.
We first started investigating pig butchering scams in 2020 in reference to faux cryptocurrency-trading cell apps that system customers had downloaded on the course of somebody the consumer had been contacted by most of the time by means of a courting app or web site. We dubbed these “CryptoRom” apps, and have continued to analysis the rip-off rings, and the way they evade platform safety on cell gadgets. One methodology that has develop into prevalent over the previous 12 months is to leverage the weaknesses of reliable cryptocurrency purposes by means of their skill to be linked to net purposes.
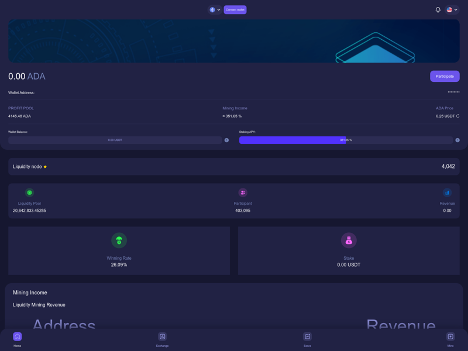
Just lately, I shared the particulars of a rip-off case during which a person sufferer (whom we known as “Frank”) misplaced over $20,000 USD in a faux “mining pool.” Based mostly on the small print Frank supplied, we have been capable of uncover a a lot bigger set of scams utilizing over a dozen completely different domains. The infrastructure of those domains was constructed on 5 completely different controlling “contract wallets” that directed cryptocurrency from victims’ wallets to different wallets for laundering. This set of scams seems to have interacted with over 90 victims. Now we have excessive confidence that the rip-off was run by three units of associates related to a multinational Chinese language-language crime group.
Wanting again to the start of 2023, I discovered these contract wallets had moved $1.22 million value of Tether (USDT) cryptocurrency from focused wallets to locations laundering the stolen crypto between January 1 and November 20. They seem to have been run by three separate menace exercise teams utilizing similar fraudulent decentralized finance (“DeFi”) app websites, suggesting that they’re a part of or affiliated with a single organized crime ring.
The ring is doubtlessly a lot bigger. I discovered traces of two different domains that matched our fingerprint for the positioning that had been deactivated earlier than I might accumulate contract information. Inspecting the wallets that acquired the funds for laundering, I discovered extra contract wallets that have been shifting scammed funds from different victims—some pointing to extra laundering wallets. I proceed to research the information to determine additional rip-off operations.
In whole, the wallets concerned within the scheme moved practically $2.9 million value of cryptocurrency this 12 months as of November 15, coming from the scams we tracked and different criminality.
Following the cash
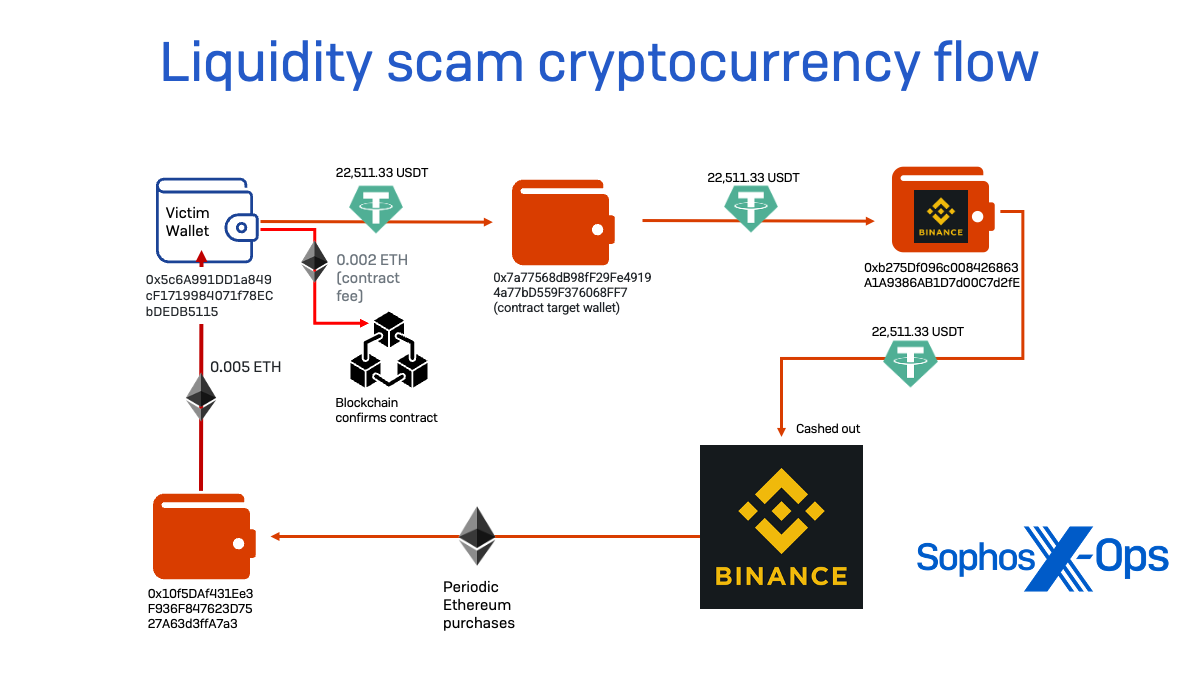
Throughout our investigation of the rip-off concentrating on “Frank,” I tracked the move of cryptocurrency from his pockets. The scammer’s entice was a faux decentralized finance app hosted on the area allnodes[.]vip—a website registered by means of and hosted by Alibaba.
The app created a wise contract—paid for in Ethereum supplied by the scammer in Frank’s case, and certain in all different scams run by this ring—that gave one other pockets handle a just about limitless “allowance,” permitting its proprietor to see the stability of the pockets being linked and to switch Tether tokens deposited within the linked pockets. This distant handle—the contract pockets—by no means moved cryptocurrency to itself however as an alternative transferred balances to different wallets underneath management of the scammers utilizing the good contract authority by authorizing transactions on the blockchain.
transactions for the management node, I used to be capable of decide that our sufferer was not the primary focused by this explicit rip-off configuration. The management node was first lively on April 5, making what could have been a take a look at switch of $55 value of Tether to verify the faux DeFi app’s configuration; the primary sufferer seems to have had funds transferred the subsequent day, being hit over the next two weeks for a complete of $15,400 value of cryptocurrency. In whole earlier than the node went quiet in early August, no less than 7 targets could be fleeced by the scammers for quantities starting from $2,000 to over $50,000—totaling $177,560.
Utilizing traits of this rip-off, I went attempting to find extra websites that have been comparable. And it shortly turned clear that this was related to a a lot bigger operation.
Attempting to find extra domains and contract wallets
By analyzing area registry information, I discovered one other area utilizing the identical branding (allnodes[.]xyz) additionally registered and hosted by means of Alibaba at a special IP handle. The websites have been similar in look and in underlying HTML and JavaScript code. The websites shared not simply the identical look, however the identical script file names and used the identical JavaScript-based in-site chat service (tawk[.]to). Nevertheless, the app on the .xyz area used a special contract pockets for its good contract payload.
I expanded my search by analyzing the online requests from every of those websites and trying to find websites with the identical JavaScript and filenames. Based mostly on these fingerprints, I discovered 11 extra domains internet hosting the identical actual code, some sharing the identical contract wallets of their configurations.
In whole, I discovered 4 addresses performing as management nodes throughout 14 domains. I additionally discovered two domains that had ceased operation however matched all traits in historic telemetry and third-party information. Inspecting the websites, I found distinct groupings of domains utilizing comparable naming conventions, area registrars and hosts, suggesting completely different sub-groups have been working similar rip-off kits concurrently. That is much like what we discovered when investigating pig butchering faux alternate websites, the place dozens of websites have been utilizing the identical code however with completely different related pockets addresses.
| Group | Area | Contract wallets | Internet hosting | Registrar | Whole Crypto quantity of transactions
(US $) |
|
|---|---|---|---|---|---|---|
| Allnodes | allnodes.vip | 0x6B79f38233726282c7F88FE670F871eAbd0c746c | Alibaba Singapore | Alibaba Cloud | 177,596.00 | |
| allnodes.xyx | 0xd2b14d2fff430a720cf44bbd064f548a585e73de | Alibaba Cloud | Alibaba Cloud | 174,934.00 | ||
| Belief | trust-oke[.}com | 0xcf6b558c218a9148cd77c04be4e3d1c1fc9d61a2 | Amazon | Amazon | 676,869.00 | |
| trust-btrust-oke[.}com | ||||||
| trust-usdt[.]com | ||||||
| trust-v2[.]com | ||||||
| trust-bnb[.]hyperlink | ||||||
| v2-eth[.]com | ||||||
| net-8897[.]com | ||||||
| Ada | ada-defi[.]pics | 0xeb7b75dd5b4b6ef7bbc6ec079cd329a782fc1efe | Cloudflare protected | Dynadot | 62,660.00 | |
| ada-defi[.]magnificence | ||||||
| ada-defi[.]xyz | ||||||
| ada-coin[.]data | ||||||
| eth-defi[.]one | ||||||
| Unknown | trust-eth[.]com | Google, then Cloudflare | Gname.com | |||
| eth-mining[.]xyz | Google, then Cloudflare | Dynadot |
As proven within the desk above, two teams of domains had shared contract pockets addresses. And thru analyzing transaction information, I discovered that each “allnodes” domains, regardless of having separate contract wallets, routed cryptocurrency to the identical locations.
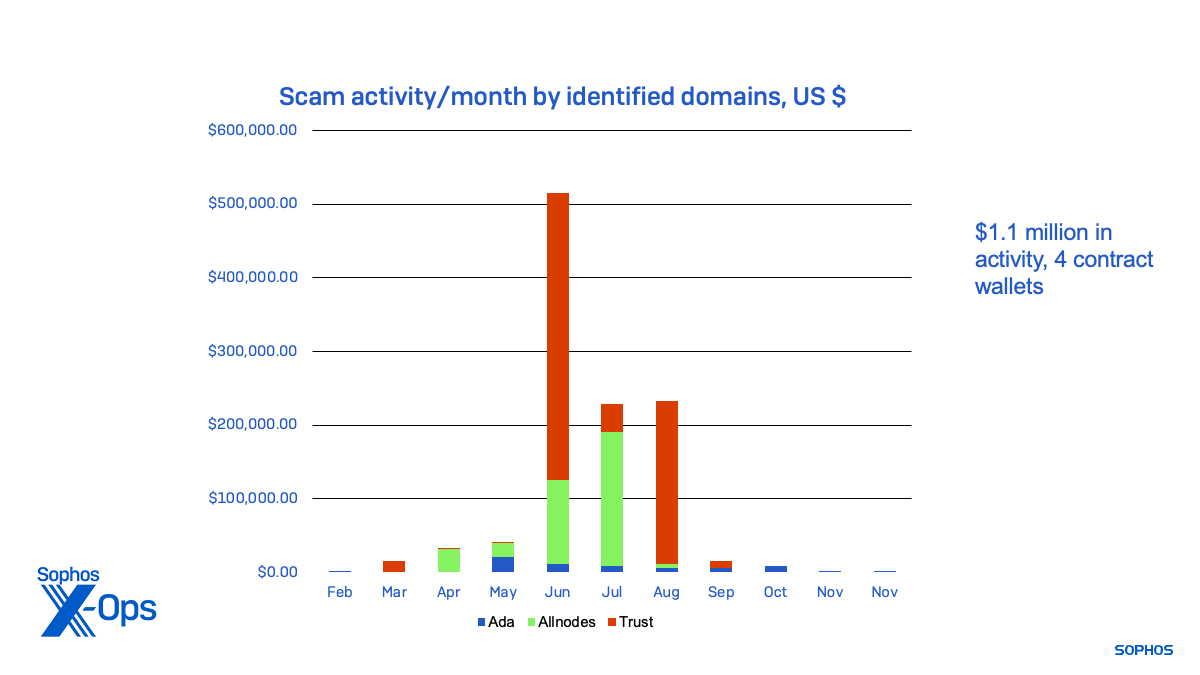
Exercise for the rip-off websites and their contract wallets, a few of which seemed to be testing the scripts related to contract wallets, dated again to February. A lot of the precise rip-off exercise related to the websites occurred in the summertime months, as proven under by the amount of cryptocurrency moved by means of every of the first contract wallets:
Additional analyzing the transaction information for the wallets receiving fraudulent withdrawals, I found extra contract wallets sending crypto following the identical sample. They have been utilizing the identical vacation spot wallets as two of the above teams:
- 0x73b970978cbf19a5e1c727de20ad73db316f3817 and 0xf12a365e53313e59E915f0e8D432a326556dD22C, related to “Belief” vacation spot pockets;
- 0x3698cc343414c69233fe580cef379f02a91bc421 , related to an “Ada” group vacation spot pockets.
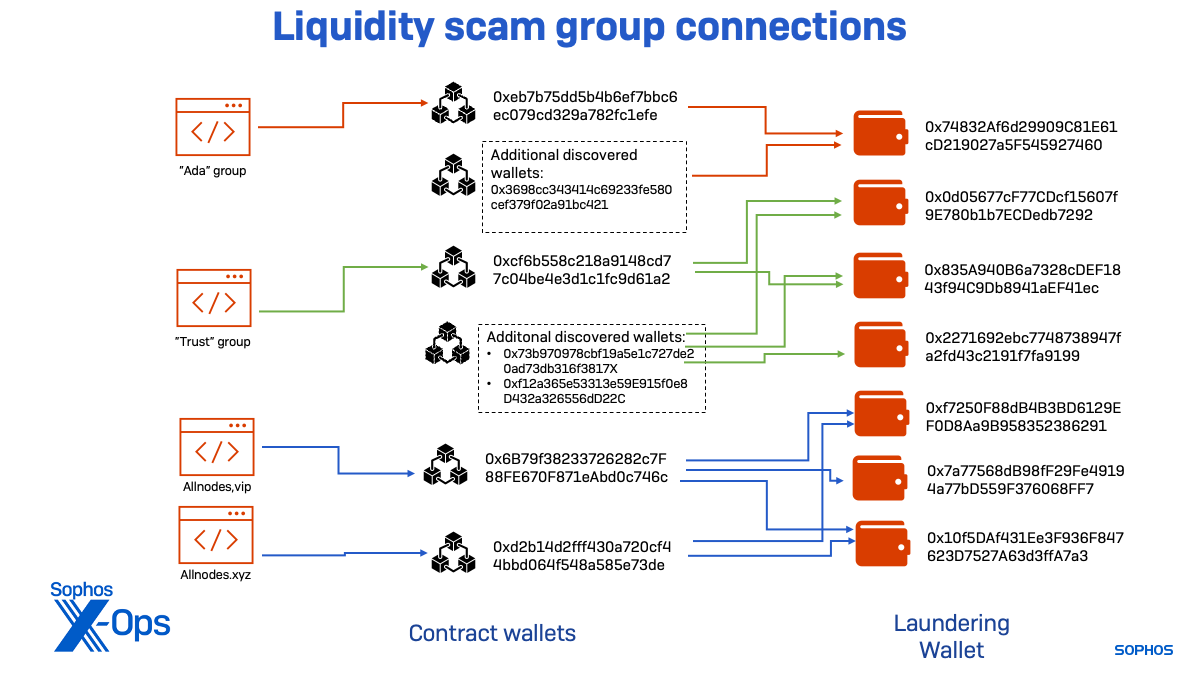
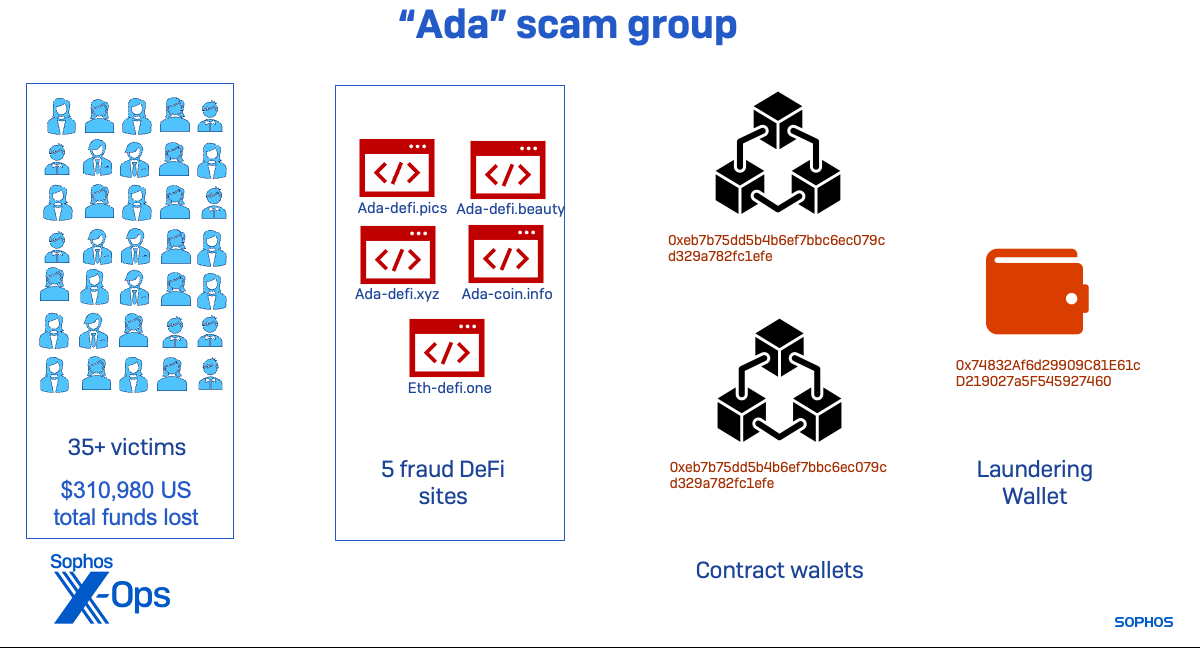
The “Ada” subgroup used a single pockets to launder funds from each its related contract wallets. This group of websites was lively starting in March, however the wallets confirmed indicators of rip-off exercise as early as February, suggesting one other area was a part of the group.
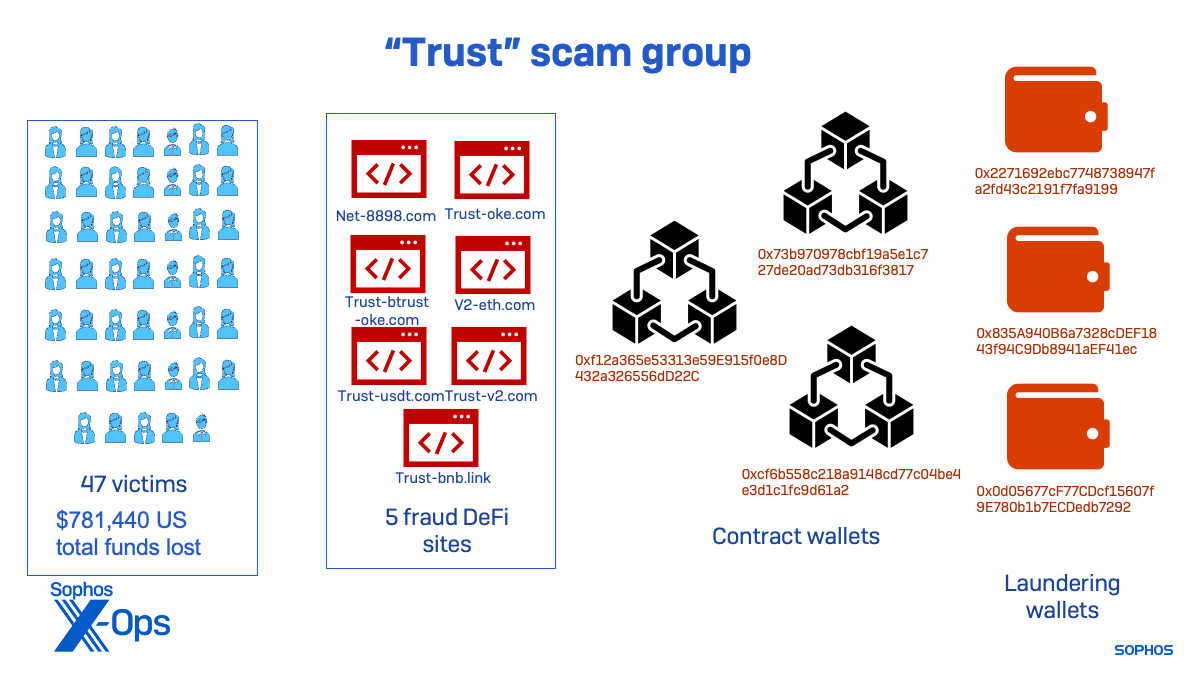
The “Belief” menace exercise cluster seems to have been lively the longest. One in all its contract wallets was extremely lively in January, indicating that one other rip-off website was lively in 2022. That pockets’s exercise fell off fully in March, with different wallets related to newer websites turning into extra lively. As of November, the “Belief” cluster was nonetheless lively, however far lower than through the peak of the rip-off websites I recognized.
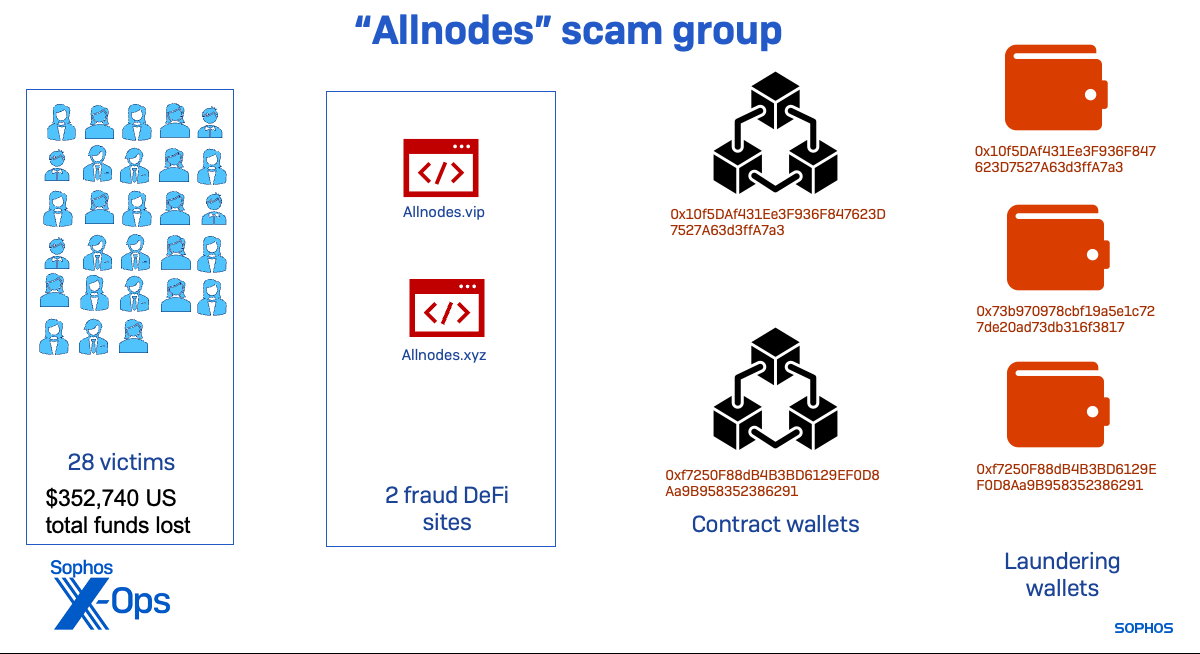
The “Allnodes” cluster was the one related to the “Frank” case. It began later than the others and shut down exercise tied to the infrastructure we recognized shortly after we have been contacted by the sufferer and commenced alerting pockets builders and exchanges of its presence. No additional money out exercise was seen on the wallets related to this menace group after August.
Regardless of being comparatively short-lived, the Allnodes group managed to usher in over $352,000 earlier than its lifecycle was ended—most of which was cashed out by means of Hong Kong financial institution accounts.
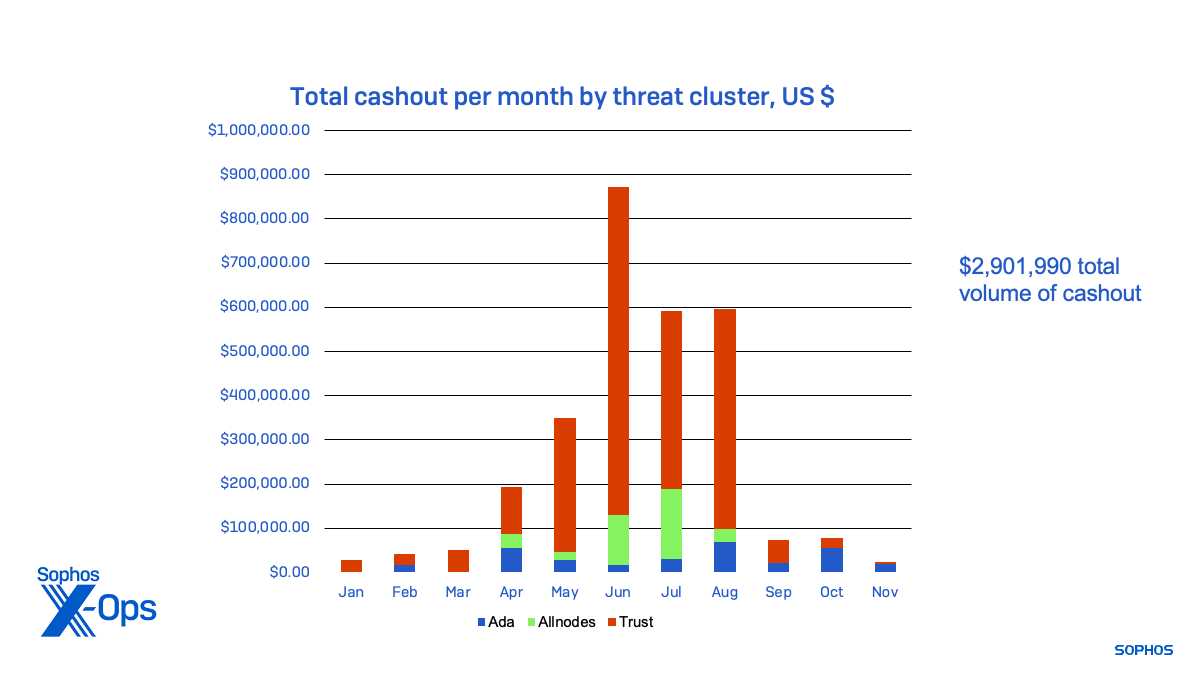 Determine 8: The funds cashed out by every of the menace exercise clusters, from January 2023 to November 2023
Determine 8: The funds cashed out by every of the menace exercise clusters, from January 2023 to November 2023
In whole, the teams utilizing the liquidity mining rip-off equipment introduced in over $2.9 million over the course of the 12 months. It’s probably that they proceed to run different, comparable scams with new infrastructure. And there are various different rip-off operations utilizing comparable techniques, instruments and practices—as I discovered investigating ideas I acquired from different rip-off victims through the course of this analysis.
Extra kits, extra scams
Following the identical strategies—attempting to find domains that used DeFi and cryptocurrency names or borrowed branding from reliable cryptocurrency-related manufacturers—we discovered a number of extra scams. One, I recognized, fronted by the area eth-defi[.]xyz, yielded one other contract pockets handle: 0x2e7e4df940a2c999bf5b5cdcd15a738b8bb462d5.
Between August 18 and November 28, that contract pockets had pulled $115,820 value of Tether cryptocurrency from victims. Nearly all of these funds have been cashed out by means of Binance.
![Figure 9: The fake liquidity mining site eth-defi[.]xyz](https://news.sophos.com/wp-content/uploads/2023/12/eth-defi-xyz.png)
Utilizing the artifacts of this website, I discovered one other 60 rip-off websites utilizing the identical equipment. I’ve not but carried out evaluation on these websites past confirming they’re working the identical rip-off interface.
As I investigated these rings, I noticed a shift in instruments and techniques by different rip-off operations—which partially seems to be pushed by the response of exchanges and pockets builders to share menace information, enabling them to dam scams on the app stage. Rip-off instrument builders are taking measures to dam harvesting of contract node information, controlling which wallets may very well be used for the rip-off, and taking higher care to evade geolocation and evaluation. These extra cautious rip-off deployments spanned lots of of domains.
One instance of this variation in rip-off website tooling—associated to a rip-off hosted at phpsqo[.]prime—got here from a sufferer. The goal, a scholar in Poland, was approached by means of WhatsApp by somebody claiming to be a Chinese language girl dwelling in Germany. The interplay led to the goal connecting her cell pockets to a contract pockets by means of that area: 0x63809823AD21B6314624621172bAf4532c5B8b72
The goal put $1,177.79 value of USDT within the pockets and noticed each day deposits till the complete stability was pulled a couple of week later.
This contract pockets was extraordinarily lively, with over 950 transactions between March 26 and November 15, so handbook evaluation of the whole variety of victims and cryptocurrency transferred remains to be in progress. However drawing from a random sampling of the transactions, I estimate the contract pockets transferred no less than $200,000 value of cryptocurrency over that interval.
Getting that information would have been troublesome with out the sufferer offering her pockets handle, as the positioning makes use of JavaScript to detect the online agent connecting and disallows desktop browsers along with checking for cryptocurrency pockets connections.:
![Figure 10: a screenshot of phpsqo[.]top showing how it appears in a desktop browser](https://news.sophos.com/wp-content/uploads/2023/12/phpsqo-top.png)
Looking on parts utilized by the positioning, I discovered 350 websites utilizing the very same equipment, most registered within the “.prime” top-level area, and all with internet hosting hid by means of Cloudflare. With out the power to passively harvest information on contract wallets related to these websites with out utilizing the kind of pockets consumer permitted by the websites, it was not attainable to get an concept of the scope of the scams related to them.
I additionally recognized by means of DNS searching one other set of about 100 websites utilizing one more mining rip-off equipment. This one permits somebody to connect with the positioning with a browser-based pockets however checks the pockets stability earlier than permitting a connection to the contract pockets. Nonetheless others use an API from WalletConnect to obscure the contract pockets handle and maintain out guests and not using a particular set of cell wallets appropriate with that service.
![Figure 11: USDmining[.]shop, another liquidity mining scam site, requires a balance in a connected wallet before the contract can be accessed](https://news.sophos.com/wp-content/uploads/2023/12/USDmining-shop.png)
Caveat Investor
When in comparison with final 12 months’s investigations, it’s clear that liquidity mining rip-off operations have matured of their methods, instruments, and practices, and that rip-off decentralized finance app “kits” have made these operations less complicated to scale up—whereas being extra accessible to much less technically-capable cybercriminals. The shifting techniques in newer kits counsel vital technical efforts are being made by instrument builders within the make use of of the Chinese language organized crime operations that again these rip-off rings.
As a result of these scams use reliable purposes which have been enabled to connect with decentralized finance purposes, the very best protection towards these ever-maturing scams stays public consciousness of the scams and wholesome skepticism towards on-line interactions. As a result of victims of pig butchering-style scams akin to these are sometimes remoted and focused by means of emotional appeals, broad public outreach is the one technique to stop or scale back loss.
We proceed to do what we are able to by reporting websites, blocking them by means of unfavourable popularity scores, and collaborating with internet hosting suppliers, regulation enforcement and cryptocurrency exchanges to get websites and alternate accounts tied to them shut down.
In the event you consider you’re a sufferer of considered one of these scams, it’s best to:
- Instantly withdraw all funds from the pockets that you simply related to the rip-off website.
- Doc every part you possibly can, together with messages between you and the attainable scammer, your cryptocurrency pockets handle, and the area you have been instructed to connect with.
- Contact regulation enforcement. Even when your case isn’t massive sufficient by itself to warrant a federal case, contact the suitable regulation enforcement company to your locality and nation (). Your information could also be useful in creating a bigger case towards rings.
- Contact the Cybercrime Help Community. They will present assets to help you in reporting crime and coping with the aftermath.
An inventory of essentially the most lately lively domains found to be related to these scams and different indicators of the rip-off operations researched right here will be discovered on our GitHub. Extra domains will probably be added as we course of them.



