Cellular Safety
WhatsApp, Telegram and Sign clones and mods stay a preferred car for malware distribution. Don’t get taken for a journey.
10 Jan 2024
•
,
5 min. learn

Cellular purposes make the world go spherical. On the spot communication companies are among the many hottest apps on iOS and Android alike – US non-profit operation Sign has an estimated 40 million customers, with the determine rising to 700 million for Telegram, one other open-source messaging service. In the meantime, Meta-owned WhatsApp is the undisputed world chief with an estimated two billion month-to-month lively customers.
However their recognition has additionally attracted the scrutiny of risk actors, eager to discover a strategy to sneak malware onto your gadget. It might find yourself costing you and even your employer expensive.
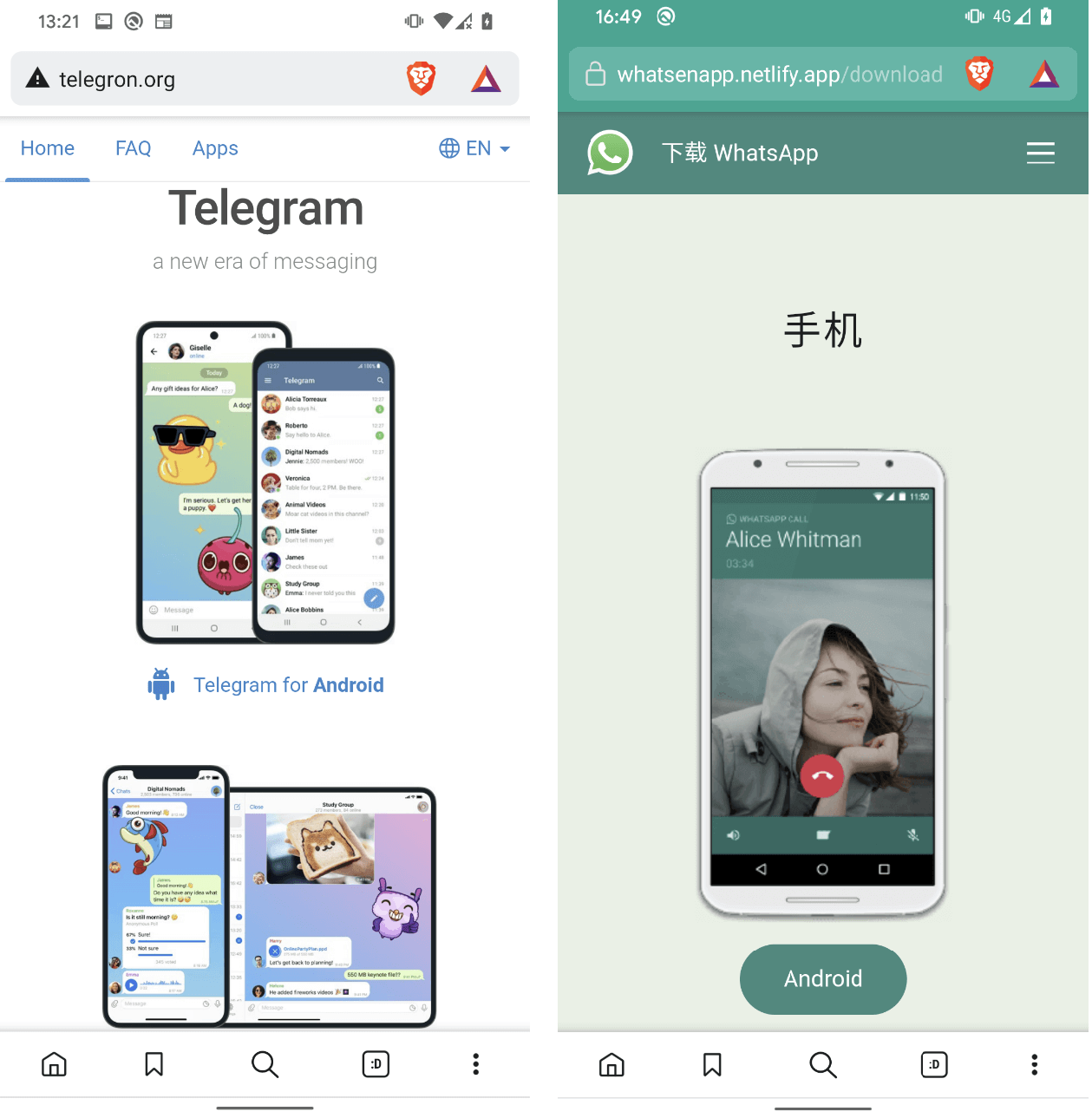
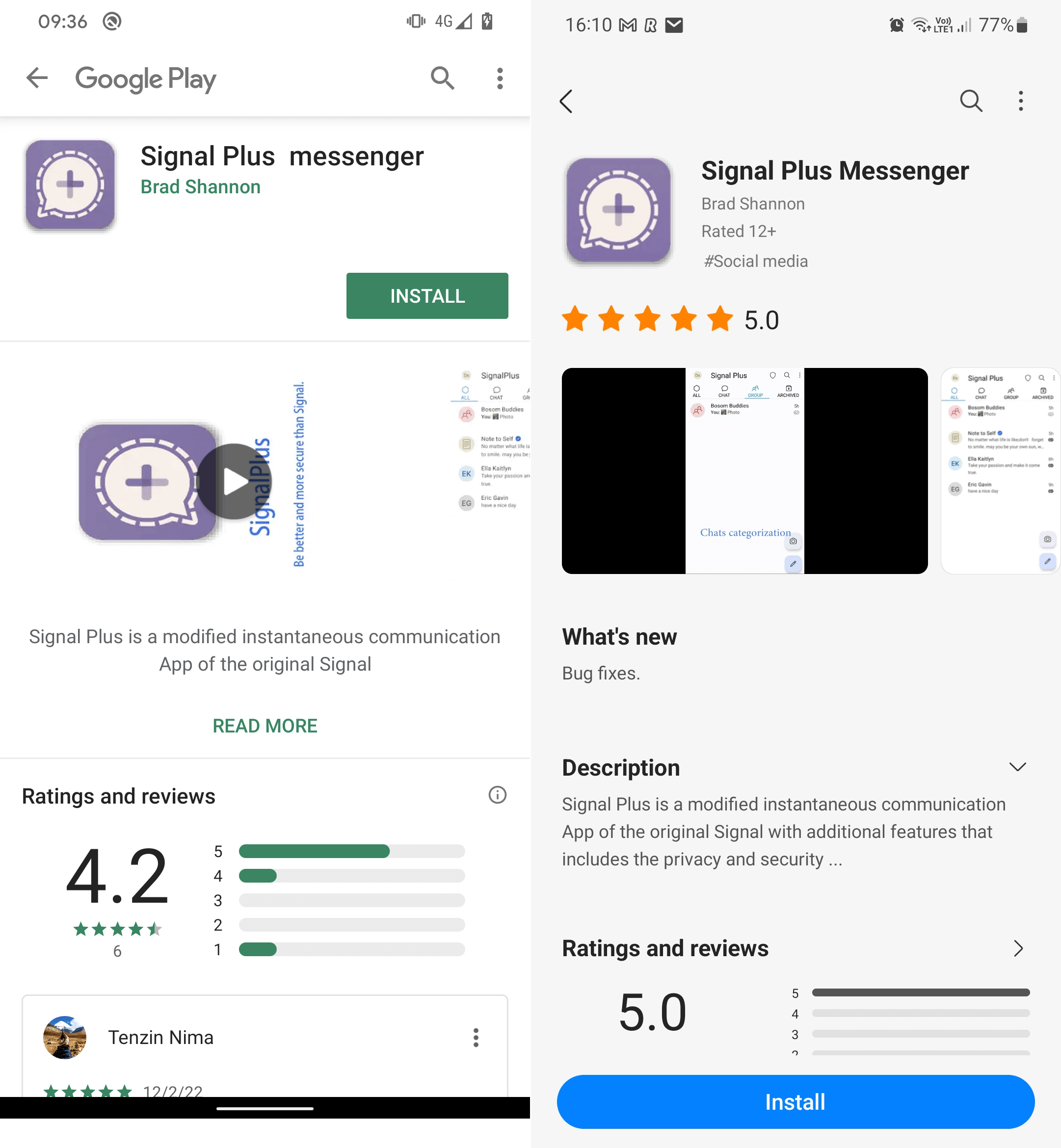
The cyber-risks of malicious copycat apps
Malicious builders have turn into fairly expert at tricking customers into downloading their wares. Usually they may produce malicious copycat apps designed to imitate respectable ones. They will then distribute them by way of phishing messages in e mail, by textual content, on social media or the communications app itself, taking the sufferer to a rip-off web page and mislead them into putting in what they consider to be an official app. Or they might direct customers to legitimate-looking faux app which will often make it by means of the strict vetting procedures on the Google Play market. Apple’s iOS platform has a far extra locked-down ecosystem and it’s even much less uncommon for malicious apps to finish up there.
At any price, for those who obtain and set up a malicious app on you telephone, it might expose you or your employer to a variety of threats together with:
- theft of delicate private information, which might be bought on the darkish net to id fraudsters
- theft of banking/monetary info, which might be used to empty funds
- efficiency points, as a result of malicious apps might change the gadget’s settings and options and sluggish it down
- adware that floods the gadget with unwatched promoting, making it troublesome to make use of
- adware designed to eavesdrop in your conversations, messages and different info
- ransomware designed to fully lock down the gadget till a price is paid
- premium-rate companies which the malware might covertly use, racking up large payments
- theft of logins for delicate accounts, which might be bought to scammers
- company cyberattacks designed to steal your work logins or information, with a view to accessing delicate company information or deploying ransomware
What ESET has seen
These threats have turn into more and more widespread over current years. Some are opportunistic assaults on a variety of shoppers, whereas others are extra extremely focused. Among the many most notable malicious copycat apps ESET has noticed embrace:
- A 2021 faux replace marketing campaign that unfold on WhatsApp, Sign and different messaging apps by way of phishing messages claiming the recipient might acquire a brand new colour theme for WhatsApp. In actuality, the WhatsApp pink theme was Trojan malware which mechanically replied to messages acquired in WhatsApp and different messaging apps with a malicious hyperlink.
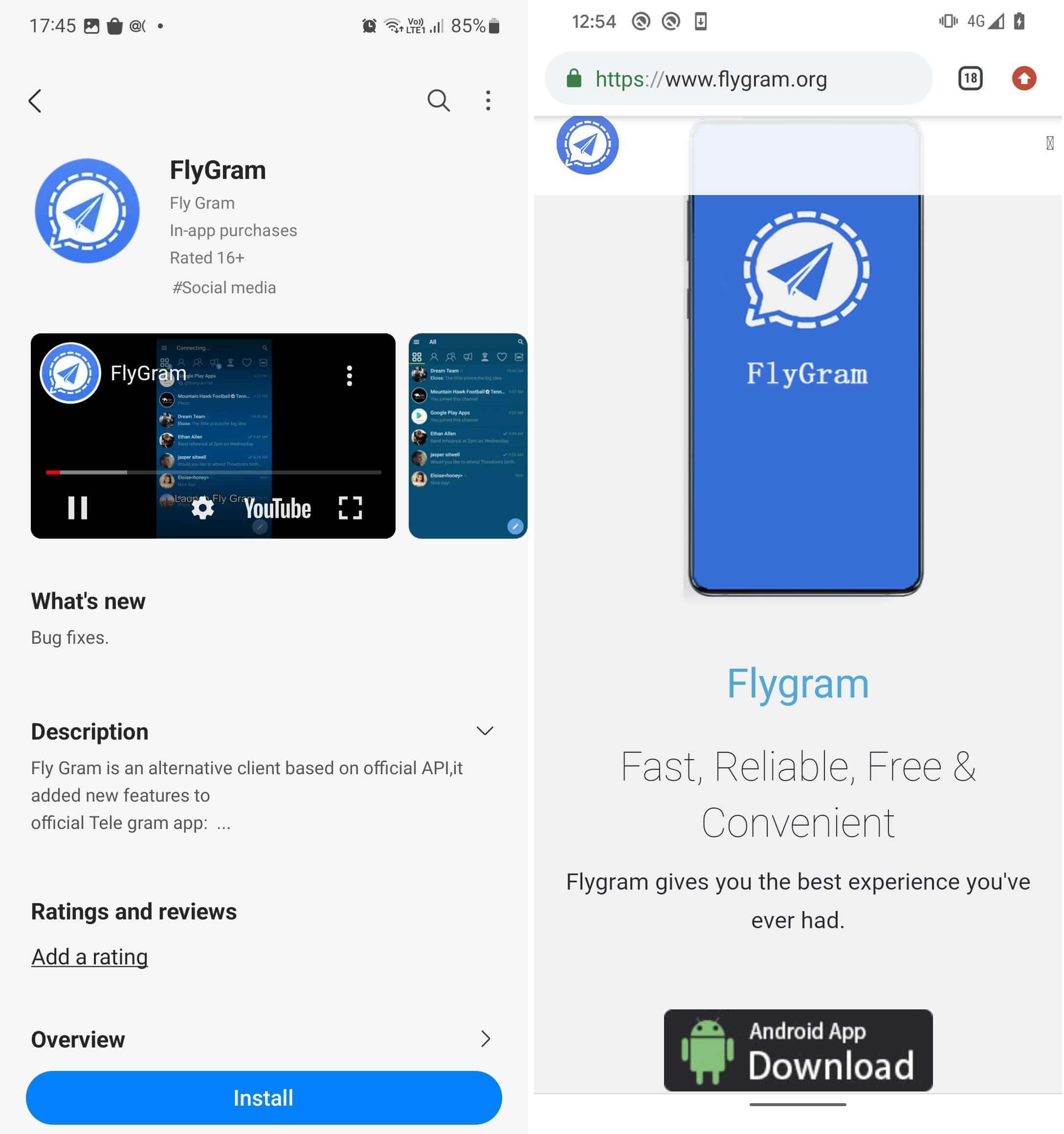
- Dozens of copycat WhatsApp and Telegram web sites touting malicious messaging apps often known as “clippers” – designed to steal or modify the contents of the gadget clipboard. Victims have been first enticed by Google Adverts resulting in fraudulent YouTube channels, which then redirected them to the copycat web sites. As soon as put in, the apps have been designed to intercept victims’ chat messages in a bid to pilfer their delicate info and cryptocurrency funds.
- China-aligned hackers hid cyberespionage malware often known as Android BadBazaar inside legitimate-looking Sign and Telegram apps. Each app sorts made it by means of official vetting and onto the Google Play and Samsung Galaxy Retailer, earlier than Google/Samsung have been made conscious of it.

Taking precautions in opposition to malicious apps
Whereas WhatsApp explicitly bans unofficial variations of its app, the open-source Telegram encourages third-party builders to create their very own Telegram purchasers. That may make discerning the true from the faux much more tough for customers. That mentioned, there are a number of issues you are able to do to cut back the probabilities of putting in one thing nasty in your gadget.
Right here’s a fast examine record:
- All the time keep on with official Android app shops, as they’ve rigorous vetting processes in place to maintain malicious apps off the platform.
- All the time preserve your cell working system and software program on the newest model as malware will usually attempt to exploit bugs in older variations.
- Earlier than downloading, all the time examine the developer’s fame on-line and any opinions for the app – watching out for point out of scams.
- Uninstall any apps that you simply don’t use, so it’s simpler to maintain monitor of what’s in your gadget.
- Don’t click on on hyperlinks or attachments, particularly if they seem in unsolicited social media messages or emails and invite you to obtain software program from third-party websites.
- Keep away from clicking on promoting on-line, in case it’s a part of a rip-off designed to steer you to a malicious copycat app.
- Be cautious of granting an app permissions that appear unrelated to its performance, because it might be malware attempting to entry your information.
- All the time use a cell safety answer from a good supplier as this can assist to dam malicious installs and/or stop malware working in your gadget.
- Think about using biometric logins fairly than mere passwords in your accounts.
- By no means obtain something from high-risk websites, similar to many grownup leisure or gaming platforms.
Learn how to spot the indicators of an imposter app
It additionally pays to be looking out for uncommon exercise in your gadget, in case malware slips by means of regardless of your finest efforts. With that in thoughts, keep in mind:
- If one thing doesn’t sound correct concerning the app’s title, description and “official app” claims, or the developer’s pedigree, likelihood is excessive you’re coping with an imposter app
- Pay attention to persistent pop-up advertisements as it could imply you’ve put in adware
- Preserve an eye fixed out for any uncommon icons in your display which can have lately been put in
- Pay attention to battery draining extra quickly than ordinary or different unusual habits
- Keep watch over payments and information utilization per thirty days; something excessively excessive might point out malicious exercise
- Perceive that in case your gadget is working slower than ordinary, it could be all the way down to malware
Smartphones and tablets are our gateway to the digital world. However it’s a world we have to safe from uninvited visitors. With these easy steps you’ll stand a a lot better likelihood of defending your funds and your private information. For a deeper dive into tips on how to cope with faux apps, learn our 7 suggestions for recognizing a faux cell app.





