A beforehand undocumented China-aligned risk actor has been linked to a set of adversary-in-the-middle (AitM) assaults that hijack replace requests from legit software program to ship a complicated implant named NSPX30.
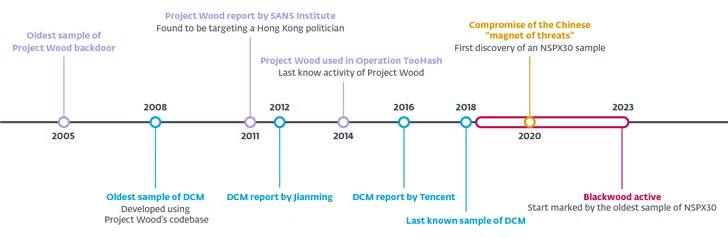
Slovak cybersecurity agency ESET is monitoring the superior persistent risk (APT) group below the identify Blackwood. It is mentioned to be lively since at the least 2018.
The NSPX30 implant has been noticed deployed through the replace mechanisms of identified software program resembling Tencent QQ, WPS Workplace, and Sogou Pinyin, with the assaults concentrating on Chinese language and Japanese manufacturing, buying and selling, and engineering corporations in addition to people situated in China, Japan, and the U.Ok.
“NSPX30 is a multistage implant that features a number of parts resembling a dropper, an installer, loaders, an orchestrator, and a backdoor,” safety researcher Facundo Muñoz mentioned. “Each of the latter two have their very own units of plugins.”
“The implant was designed across the attackers’ functionality to conduct packet interception, enabling NSPX30 operators to cover their infrastructure.”
The origins of the backdoor, which can be able to bypassing a number of Chinese language anti-malware options by allowlisting itself, may be traced to a different malware from January 2005 codenamed Challenge Wooden, which is designed to reap system and community info, report keystrokes, and take screenshots from sufferer techniques.
Challenge Wooden’s codebase has acted as the muse for a number of implants, together with spawning variants like DCM (aka Darkish Specter) in 2008, with the malware subsequently utilized in assaults concentrating on people of curiosity in Hong Kong and the Higher China space in 2012 and 2014.
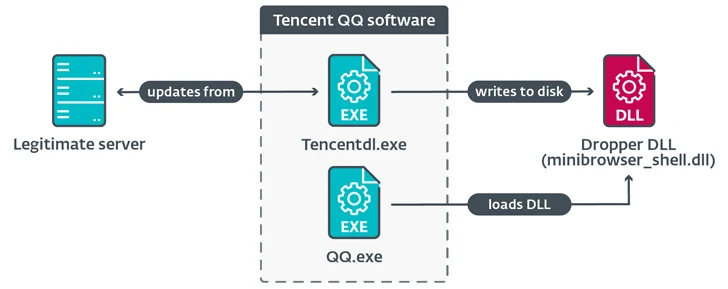
NSPX30, the newest iteration of the implant, is delivered when makes an attempt to obtain software program updates from legit servers utilizing the (unencrypted) HTTP protocol ends in a system compromise, paving the best way for the deployment of a dropper DLL file.
The malicious dropper deployed as a part of the compromised replace course of creates a number of recordsdata on disk and executes “RsStub.exe,” a binary related to the Rising Antivirus software program in order to launch “comx3.dll” by benefiting from the very fact the previous is vulnerable to DLL side-loading.
“comx3.dll” capabilities as a loader to execute a 3rd file named “comx3.dll.txt,” which is an installer library chargeable for activating the next-stage assault chain that culminates within the execution of the orchestrator element (“WIN.cfg”).
It is presently not identified how the risk actors ship the dropper within the type of malicious updates, however Chinese language risk actors like BlackTech, Evasive Panda, and Mustang Panda have leveraged compromised routers as a channel to distribute malware previously.
ESET speculates that the attackers “are deploying a community implant within the networks of the victims, probably on weak community home equipment resembling routers or gateways.”
“The truth that we discovered no indications of site visitors redirection through DNS would possibly point out that when the hypothesized community implant intercepts unencrypted HTTP site visitors associated to updates, it replies with the NSPX30 implant’s dropper within the type of a DLL, an executable file, or a ZIP archive containing the DLL.”
The orchestrator then proceeds to create two threads, one to acquire the backdoor (“msfmtkl.dat”) and one other to load its plugins and add exclusions to allowlist the loader DLLs to bypass Chinese language anti-malware options.
The backdoor is downloaded through an HTTP request to Baidu’s web site www.baidu[.]com, a legit Chinese language search engine, with an uncommon Consumer-Agent string that masquerades the request as originating from the Web Explorer browser on Home windows 98.
The response from the server is then saved to a file from which the backdoor element is extracted and loaded into reminiscence.
NSPX30, as a part of its initialization section, additionally creates a passive UDP listening socket for receiving instructions from the controller and exfiltrating information by probably intercepting DNS question packets with a purpose to anonymize its command-and-control (C2) infrastructure.
The directions permit the backdoor to create a reverse shell, acquire file info, terminate particular processes, seize screenshots, log keystrokes, and even uninstall itself from the contaminated machine.
The disclosure comes weeks after SecurityScorecard revealed new infrastructure related to a different Beijing-nexus cyber espionage group often called Volt Hurricane (aka Bronze Silhouette) that leverages a botnet created by exploiting identified safety flaws in end-of-life Cisco RV320/325 routers (CVE-2019-1652 and CVE-2019-1653) working throughout Europe, North America, and Asia Pacific.
“Roughly 30% of them (325 of 1,116 units) communicated with two IP addresses beforehand named as proxy routers used for command-and-control (C2) communications, 174.138.56[.]21 and 159.203.113[.]25, in a thirty-day interval,” the corporate mentioned.
“Volt Hurricane might intention to make use of these compromised units to switch stolen information or join to focus on organizations’ networks.”