SolarWinds fixes critical RCE bugs in access rights audit solution
SolarWinds has patched five remote code execution (RCE) flaws in its Access Rights Manager (ARM) solution, including three critical severity vulnerabilities that allow unauthenticated exploitation. Access Rights Manager allows companies to manage and audit access rights across their IT infrastructure to minimize insider threat impact and more. CVE-2024-23476 and CVE-2024-23479 are due to path traversal […]
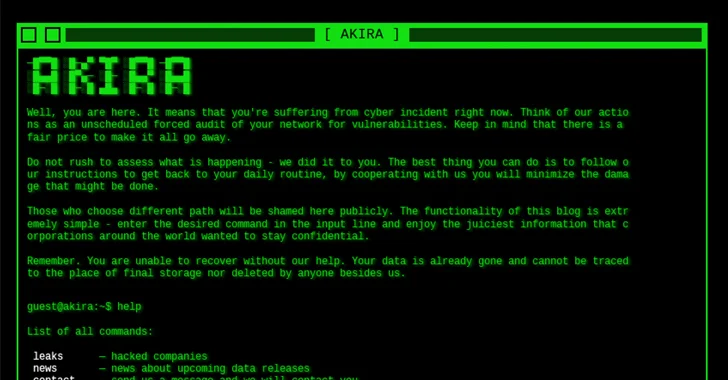
Akira Ransomware Exploiting Cisco ASA/FTD Vulnerability
Feb 16, 2024NewsroomRansomware / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched security flaw impacting Cisco Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software to its Known Exploited Vulnerabilities (KEV) catalog, following reports that it’s being likely exploited in Akira ransomware attacks. The vulnerability in question is […]
Major Tech Firms Develop ‘Tech Accord’ to Combat AI Deepfakes
In what is being referred to as a “Tech Accord,” major technology companies are showing that they are willing to work together in order to combat artificial intelligence (AI)-generated content that could threaten democratic elections globally this year. The draft of the accord will be presented at the Munich Security Conference, which begins today, and […]
Juniper Support Portal Exposed Customer Device Info – Krebs on Security
Until earlier this week, the support website for networking equipment vendor Juniper Networks was exposing potentially sensitive information tied to customer products, including which devices customers bought, as well as each product’s warranty status, service contracts and serial numbers. Juniper said it has since fixed the problem, and that the inadvertent data exposure stemmed from […]
How digital forensics unlocks the truth
The burgeoning field of digital forensics plays a crucial role in investigating a wide range of cybercrimes and cybersecurity incidents. Indeed, in our technology-centric world, even investigations of ‘traditional’ crimes often include an element of digital evidence that is waiting to be retrieved and analyzed. This art of uncovering, analyzing and interpreting digital evidence has […]
This Complete Ethical Hacking Bundle Is Less Than $40
As cybercrime has grown over the past few years, the demand for ethical hackers has reached a new height. These security specialists are paid to break into corporate networks and systems to expose vulnerabilities, thereby finding what needs to be patched up and protected. It’s a lucrative career, and whether you’re looking for ways to […]
Valentine’s Alert: Don’t Let Scammers Break Your Heart or Your Bank Account
As with any major holiday or special occasion, Valentine’s Day is unfortunately not immune to scammers looking for an opportunity to exploit unsuspecting individuals. Their deceitful acts can break hearts and bank accounts. In this article, we spotlight some common Valentine’s Day scams, offer tips on how to protect yourself, and navigate this romantic day […]