Cybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
Feb 22, 2024NewsroomNetwork Security / Penetration Testing A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying worm that leverages SSH credentials discovered on a compromised system to start spreading itself throughout the network,” Sysdig researcher Miguel Hernández said. “The worm automatically searches […]
‘VoltSchemer’ Hack Allows Wireless Charger Takeovers
Researchers from the University of Florida, alongside CertiK, have come up with a theoretical attack, called “VoltSchemer” (PDF), that allows for wireless charger takeover through power supply voltage manipulation. The attack could allow threat actors to damage charging devices, bypass Qi standard’s mechanisms, and manipulate voice assistants. It would be able to do this by […]
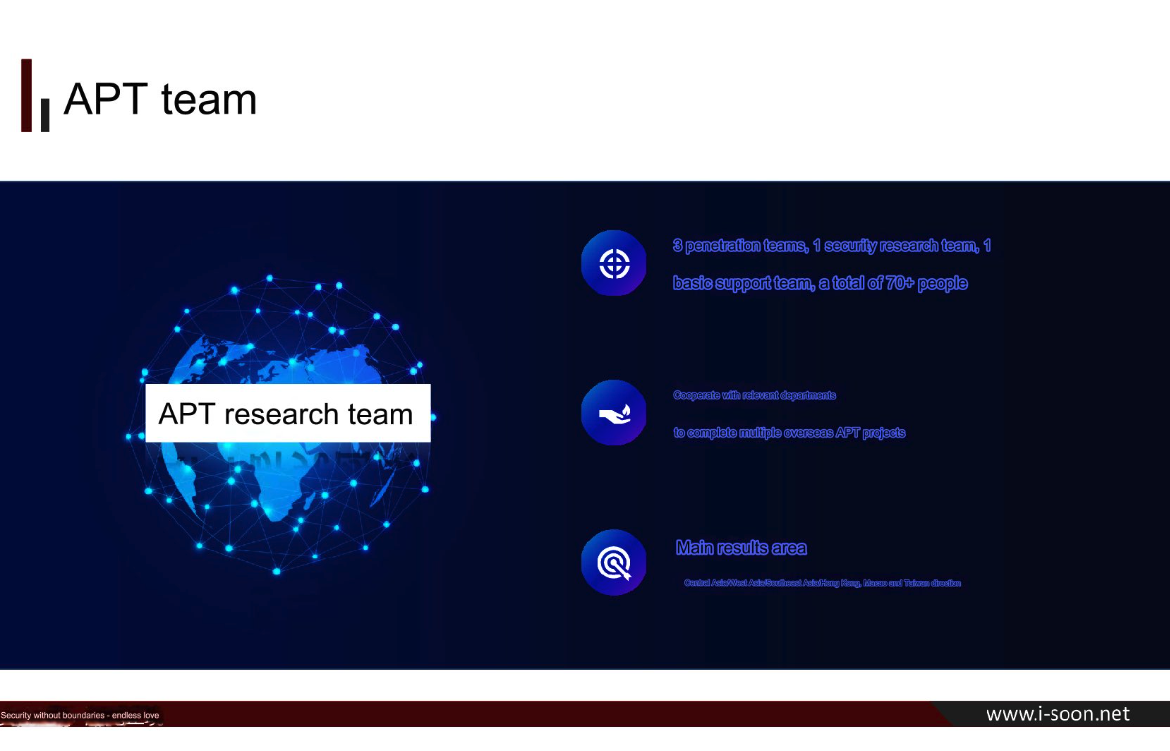
New Leak Shows Business Side of China’s APT Menace – Krebs on Security
A new data leak that appears to have come from one of China’s top private cybersecurity firms provides a rare glimpse into the commercial side of China’s many state-sponsored hacking groups. Experts say the leak illustrates how Chinese government agencies increasingly are contracting out foreign espionage campaigns to the nation’s burgeoning and highly competitive cybersecurity […]
Top 4 Ivanti Competitors and Alternatives for 2024
Ivanti Secure VPN is a popular remote access VPN solution used by businesses, organizations and governments worldwide. Unfortunately, five new zero-day vulnerabilities in Ivanti have been discovered this year, which allow an unauthenticated attacker to execute remote code and compromise systems. French cyberdefense search engine ONYPHE has said that 29,664 Ivanti Secure VPN appliances are […]
Cleanup on Aisle Six! How to Close Online Accounts for Savings and Security.
How many online accounts do you have? Dozens? Hundreds? You probably have more than you think, and deleting a bunch of them might be the right call. You have two good reasons: savings and security. Certainly, you have trusted accounts you use all the time, like the one with your bank and a few […]
The AI Threat Landscape: Tech Companies and Governments Must Unite Behind Cybersecurity in 2024
Tech companies and governments will join forces to develop advanced AI detection systems, ensuring a safer online environment. Human ingenuity boosted by AI capabilities offers new pathways to address complex societal problems—such as more efficient agricultural production, medical research, and sustainable energy production. AI may even harness the power of networks at scale to finally […]
Lessons learned on winning the war on cybercrime – Sophos News
Late on February 19, 2024, the main website of LockBit, the most prolific ransomware group in recent memory, was seized by the United Kingdom’s National Crime Agency (NCA). In cooperation with their international law enforcement partners at the United States FBI, the French Gendarmerie National, Europol, and others, the NCA seized the physical servers that […]