From Military Kid to Product Marketing: My McAfee Journey
Employee Spotlight: Meet Jovohn! From military beginnings to mobile security champion, meet Jovohn, our passionate Product Marketer and MAHC President. Discover how his unique path led him to advocate for customer safety and drive innovation in McAfee’s mobile business. Can you tell us a bit about yourself and your role at McAfee? Absolutely! I’m a […]
Mitigating Lateral Movement with Zero Trust Access
Security service edge (SSE) technology was created to protect remote and branch users with a unified, cloud-delivered security stack. To understand how SSE solutions protect organizations and their users, it’s worthwhile to analyze attacker techniques, as well as the protections and controls SSE solutions use to disrupt them. It’s useful to use the MITRE ATT&CK […]
Exploring host discovery techniques in a network
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. In a network assessment, one of the first tasks is to narrow down a large set of IP addresses to a list of […]
The Impact of Organizational Structure on Cybersecurity Outcomes – Sophos News
Cybersecurity professionals are a core element of an organization’s cyber defenses. While much has been written about the shortage of skilled cybersecurity staff, far less focus has been given to how to enable these professionals to make the greatest impact. In short, how best to set them up for success. Our recent analysis aims to […]
ScreenConnect flaws exploited to drop new ToddleShark malware
The North Korean APT hacking group Kimsuky is exploiting ScreenConnect flaws, particularly CVE-2024-1708 and CVE-2024-1709, to infect targets with a new malware variant dubbed ToddleShark. Kimsuky (aka Thallium and Velvet Chollima) is a North Korean state-sponsored hacking group known for cyber espionage attacks on organizations and governments worldwide. The threat actors are exploiting authentication bypass […]
What is Exposure Management and How Does it Differ from ASM?
Mar 05, 2024NewsroomAttack Surface / Exposure Management Startups and scales-ups are often cloud-first organizations and rarely have sprawling legacy on-prem environments. Likewise, knowing the agility and flexibility that cloud environments provide, the mid-market is predominantly running in a hybrid state, partly in the cloud but with some on-prem assets. While there has been a bit […]
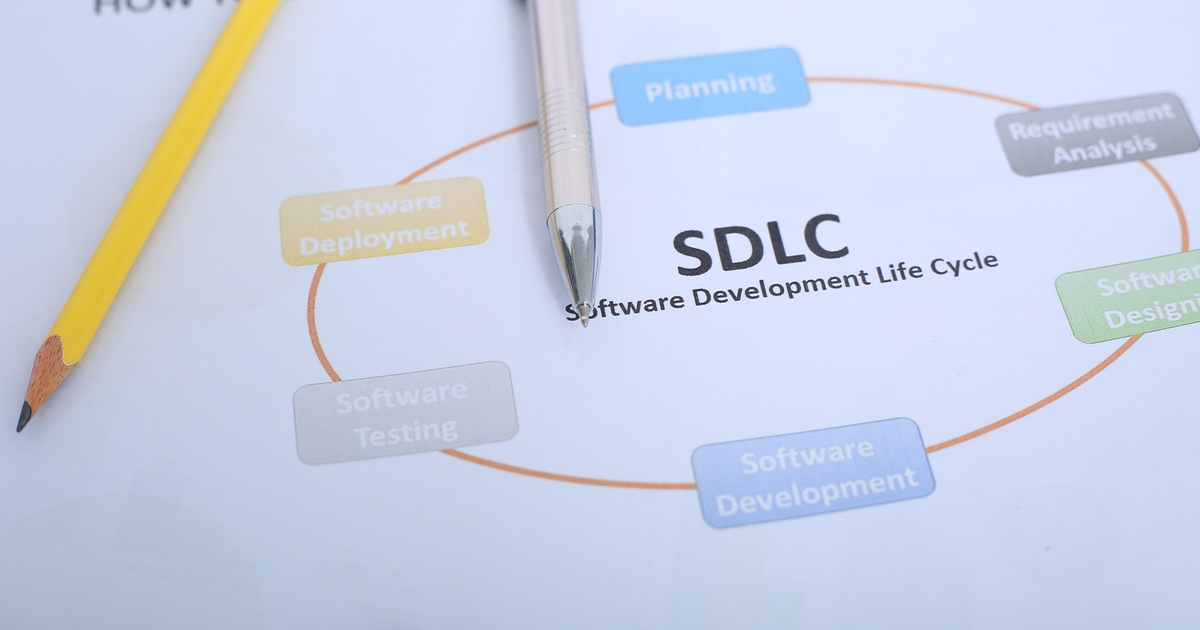
Critical TeamCity Bugs Endanger Software Supply Chain
Cloud versions of the JetBrains TeamCity software development platform manager have already been updated against a new pair of critical vulnerabilities, but on-premises deployments need immediate patching, a security advisory from the vendor warned this week. This is the second round of critical TeamCity vulnerabilities in the past two months. The ramifications could be wide: […]