Android is the primary cellular working system to introduce superior mobile safety mitigations for each customers and enterprises. Android 14 introduces help for IT directors to disable 2G help of their managed machine fleet. Android 14 additionally introduces a function that disables help for null-ciphered mobile connectivity.
Hardening community safety on Android
The Android Safety Mannequin assumes that each one networks are hostile to maintain customers protected from community packet injection, tampering, or eavesdropping on person site visitors. Android doesn’t depend on link-layer encryption to deal with this menace mannequin. As a substitute, Android establishes that each one community site visitors must be end-to-end encrypted (E2EE).
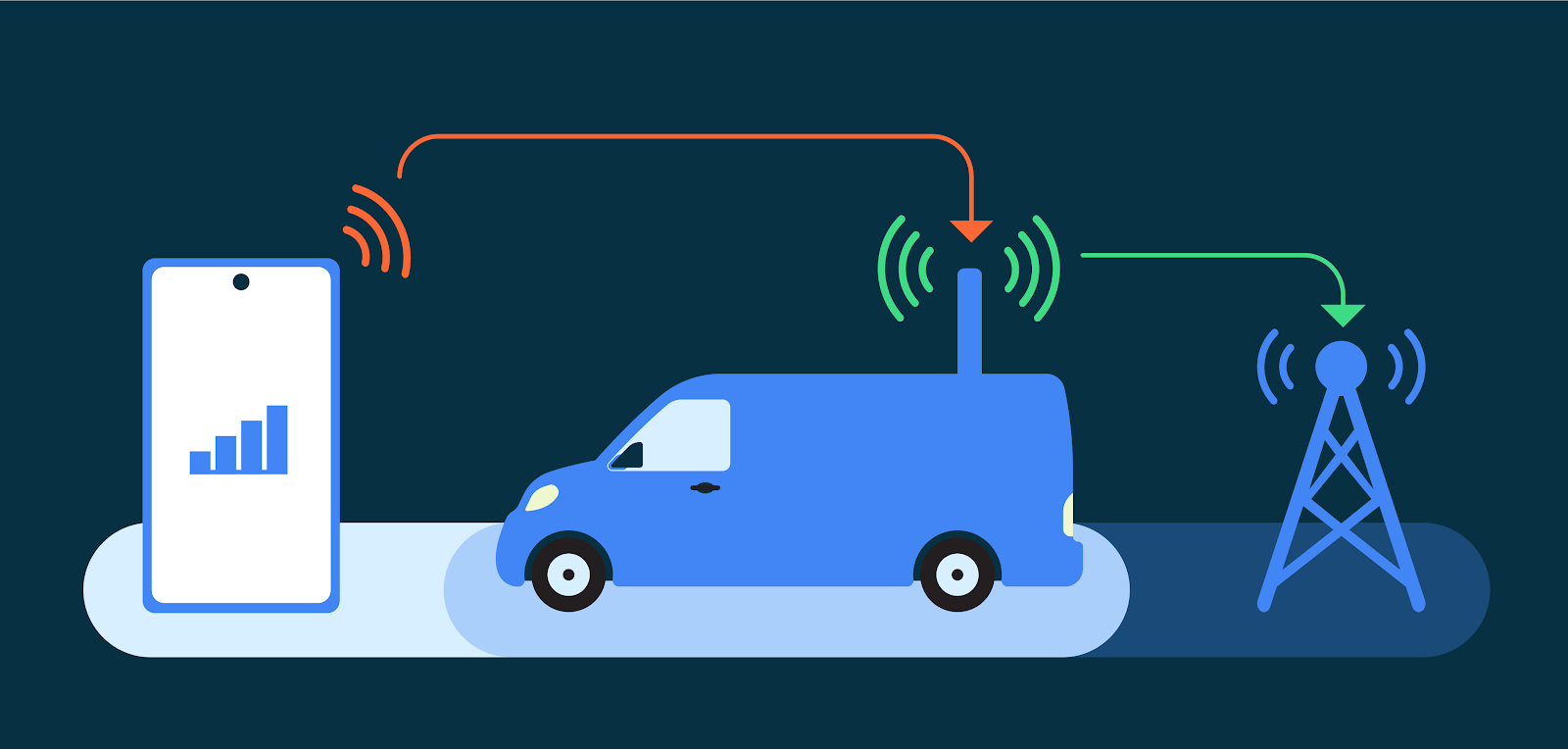
When a person connects to mobile networks for his or her communications (knowledge, voice, or SMS), as a result of distinctive nature of mobile telephony, the hyperlink layer presents distinctive safety and privateness challenges. False Base Stations (FBS) and Stingrays exploit weaknesses in mobile telephony requirements to trigger hurt to customers. Moreover, a smartphone can not reliably know the legitimacy of the mobile base station earlier than making an attempt to hook up with it. Attackers exploit this in plenty of methods, starting from site visitors interception and malware sideloading, to stylish dragnet surveillance.
Recognizing the far reaching implications of those assault vectors, particularly for at-risk customers, Android has prioritized hardening mobile telephony. We’re tackling well-known insecurities such because the danger introduced by 2G networks, the chance introduced by null ciphers, different false base station (FBS) threats, and baseband hardening with our ecosystem companions.
2G and a historical past of inherent safety danger
The cellular ecosystem is quickly adopting 5G, the newest wi-fi commonplace for cellular, and plenty of carriers have began to show down 2G service. In the USA, for instance, most main carriers have shut down 2G networks. Nevertheless, all present cellular units nonetheless have help for 2G. Because of this, when out there, any cellular machine will connect with a 2G community. This happens mechanically when 2G is the one community out there, however this will also be remotely triggered in a malicious assault, silently inducing units to downgrade to 2G-only connectivity and thus, ignoring any non-2G community. This conduct occurs no matter whether or not native operators have already sundown their 2G infrastructure.
2G networks, first carried out in 1991, don’t present the identical stage of safety as subsequent cellular generations do. Most notably, 2G networks based mostly on the International System for Cell Communications (GSM) commonplace lack mutual authentication, which permits trivial Particular person-in-the-Center assaults. Furthermore, since 2010, safety researchers have demonstrated trivial over-the-air interception and decryption of 2G site visitors.
The out of date safety of 2G networks, mixed with the power to silently downgrade the connectivity of a tool from each 5G and 4G all the way down to 2G, is the most typical use of FBSs, IMSI catchers and Stingrays.
Stingrays are obscure but very highly effective surveillance and interception instruments which were leveraged in a number of eventualities, starting from doubtlessly sideloading Pegasus malware into journalist telephones to a subtle phishing scheme that allegedly impacted a whole bunch of 1000’s of customers with a single FBS. This Stingray-based fraud assault, which probably downgraded machine’s connections to 2G to inject SMSishing payloads, has highlighted the dangers of 2G connectivity.
To deal with this danger, Android 12 launched a new function that permits customers to disable 2G on the modem stage. Pixel 6 was the primary machine to undertake this function and it’s now supported by all Android units that conform to Radio HAL 1.6+. This function was rigorously designed to make sure that customers will not be impacted when making emergency calls.
Mitigating 2G safety dangers for enterprises
The trade acknowledged the numerous safety and privateness advantages and influence of this function for at-risk customers, and we acknowledged how crucial disabling 2G is also for our Android Enterprise clients.
Enterprises that use smartphones and tablets require sturdy safety to safeguard delicate knowledge and Mental Property. Android Enterprise supplies strong administration controls for connectivity security capabilities, together with the power to disable WiFi, Bluetooth, and even knowledge signaling over USB. Beginning in Android 14, enterprise clients and authorities businesses managing units utilizing Android Enterprise will be capable to limit a tool’s skill to downgrade to 2G connectivity.
The 2G safety enterprise management in Android 14 permits our clients to configure cellular connectivity based on their danger mannequin, permitting them to guard their managed units from 2G site visitors interception, Particular person-in-the-Center assaults, and different 2G-based threats. IT directors can configure this safety as obligatory, at all times holding the 2G radio off or guaranteeing staff are protected when touring to particular high-risk areas.
These new capabilities are a part of the great set of 200+ administration controls that Android supplies IT directors by way of Android Enterprise. Android Enterprise additionally supplies complete audit logging with over 80 occasions together with these new administration controls. Audit logs are a crucial a part of any group’s safety and compliance technique. They supply an in depth document of all exercise on a system, which can be utilized to trace down unauthorized entry, establish safety breaches, and troubleshoot system issues.
Additionally in Android 14
The upcoming Android launch additionally tackles the chance of mobile null ciphers. Though all IP-based person site visitors is protected and E2EE by the Android platform, mobile networks expose circuit-switched voice and SMS site visitors. These two explicit site visitors varieties are strictly protected solely by the mobile hyperlink layer cipher, which is totally managed by the community with out transparency to the person. In different phrases, the community decides whether or not site visitors is encrypted and the person has no visibility into whether or not it’s being encrypted.
Current stories recognized utilization of null ciphers in industrial networks, which exposes person voice and SMS site visitors (reminiscent of One-Time Password) to trivial over the air interception. Furthermore, some industrial Stingrays present performance to trick units into believing ciphering just isn’t supported by the community, thus downgrading the connection to a null cipher and enabling site visitors interception.
Android 14 introduces a person choice to disable help, on the modem-level, for null-ciphered connections. Equally to 2G controls, it’s nonetheless doable to position emergency calls over an unciphered connection. This performance will enormously enhance communication privateness for units that undertake the newest radio {hardware} abstraction layer (HAL). We count on this new connectivity safety function to be out there in additional units over the following few years as it’s adopted by Android OEMs.
Persevering with to companion to boost the trade bar for mobile safety
Alongside our Android-specific work, the group is usually concerned within the improvement and enchancment of mobile safety requirements. We actively take part in requirements our bodies reminiscent of GSMA Fraud and Safety Group in addition to the third Era Partnership Challenge (3GPP), notably its safety and privateness group (SA3). Our long-term purpose is to render FBS threats out of date.
Specifically, Android safety is main a brand new initiative inside GSMA’s Fraud and Safety Group (FASG) to discover the feasibility of contemporary id, belief and entry management methods that may allow radically hardening the safety of telco networks.
Our efforts to harden mobile connectivity undertake Android’s defense-in-depth technique. We usually companion with different inner Google groups as properly, together with the Android Pink Group and our Vulnerability Rewards Program.
Furthermore, in alignment with Android’s openness in safety, we actively companion with prime educational teams in mobile safety analysis. For instance, in 2022 we funded through our Android Safety and Privateness Analysis grant (ASPIRE) a challenge to develop a proof-of-concept to judge mobile connectivity hardening in smartphones. The educational group introduced the end result of that challenge within the final ACM Convention on Safety and Privateness in Wi-fi and Cell Networks.
The safety journey continues
Person safety and privateness, which incorporates the security of all person communications, is a precedence on Android. With upcoming Android releases, we are going to proceed so as to add extra options to harden the platform towards mobile safety threats.
We sit up for discussing the way forward for telco community safety with our ecosystem and trade companions and standardization our bodies. We may also proceed to companion with educational establishments to resolve advanced issues in community safety. We see large alternatives to curb FBS threats, and we’re excited to work with the broader trade to resolve them.
Particular due to our colleagues who had been instrumental in supporting our mobile community safety efforts: Nataliya Stanetsky, Robert Greenwalt, Jayachandran C, Gil Cukierman, Dominik Maier, Alex Ross, Il-Sung Lee, Kevin Deus, Farzan Karimi, Xuan Xing, Wes Johnson, Thiébaud Weksteen, Pauline Anthonysamy, Liz Louis, Alex Johnston, Kholoud Mohamed, Pavel Grafov