A now-patched safety flaw in Microsoft Outlook could possibly be exploited by risk actors to entry NT LAN Supervisor (NTLM) v2 hashed passwords when opening a specifically crafted file.
The problem, tracked as CVE-2023-35636 (CVSS rating: 6.5), was addressed by the tech large as a part of its Patch Tuesday updates for December 2023.
“In an electronic mail assault situation, an attacker might exploit the vulnerability by sending the specifically crafted file to the person and convincing the person to open the file,” Microsoft mentioned in an advisory launched final month.
In a web-based assault situation, an attacker might host a web site (or leverage a compromised web site that accepts or hosts user-provided content material) containing a specifically crafted file designed to take advantage of the vulnerability.”
Put in a different way, the adversary must persuade customers to click on a hyperlink, both embedded in a phishing electronic mail or despatched by way of an prompt message, after which deceive them into opening the file in query.
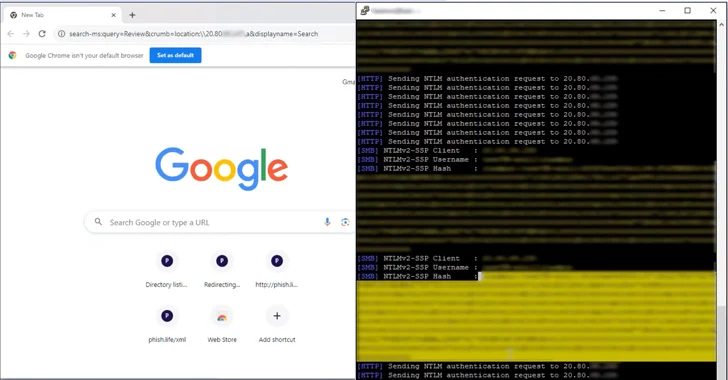
CVE-2023-35636 is rooted within the calendar-sharing operate within the Outlook electronic mail utility, whereby a malicious electronic mail message is created by inserting two headers “Content material-Class” and “x-sharing-config-url” with crafted values with the intention to expose a sufferer’s NTLM hash throughout authentication.
Varonis safety researcher Dolev Taler, who has been credited with discovering and reporting the bug, mentioned NTLM hashes could possibly be leaked by leveraging Home windows Efficiency Analyzer (WPA) and Home windows File Explorer. These two assault strategies, nevertheless, stay unpatched.
“What makes this fascinating is that WPA makes an attempt to authenticate utilizing NTLM v2 over the open net,” Taler mentioned.
“Often, NTLM v2 ought to be used when trying to authenticate in opposition to inside IP-address-based companies. Nevertheless, when the NTLM v2 hash is passing by the open web, it’s susceptible to relay and offline brute-force assaults.”
The disclosure comes as Examine Level revealed a case of “pressured authentication” that could possibly be weaponized to leak a Home windows person’s NTLM tokens by tricking a sufferer into opening a rogue Microsoft Entry file.
Microsoft, in October 2023, introduced plans to discontinue NTLM in Home windows 11 in favor of Kerberos for improved safety owing to the truth that it doesn’t help cryptographic strategies and is prone to relay assaults.